Sécurité de la couche de transport
Transport Layer Security ( TLS ), le successeur de Secure Sockets Layer ( SSL ), désormais obsolète, est un protocole cryptographique conçu pour assurer la sécurité des communications sur un réseau informatique. Le protocole est largement utilisé dans des applications telles que la messagerie électronique , la messagerie instantanée et la voix sur IP , mais son utilisation pour sécuriser HTTPS reste la plus visible publiquement.
Le protocole TLS vise principalement à assurer la cryptographie , y compris la confidentialité (confidentialité), l’intégrité et l’authenticité grâce à l’utilisation de certificats , entre deux ou plusieurs applications informatiques communicantes. Il s’exécute dans la couche application et est lui-même composé de deux couches : l’enregistrement TLS et les protocoles de prise de contact TLS .
TLS est une norme proposée par l’Internet Engineering Task Force (IETF), définie pour la première fois en 1999, et la version actuelle est TLS 1.3, définie en août 2018. TLS s’appuie sur les spécifications SSL antérieures (1994, 1995, 1996) développées par Netscape Communications pour ajoutant le protocole HTTPS à leur navigateur Web Navigator.
La description
Les applications client-serveur utilisent le protocole TLS pour communiquer sur un réseau d’une manière conçue pour empêcher l’écoute clandestine et la falsification .
Comme les applications peuvent communiquer avec ou sans TLS (ou SSL), il est nécessaire que le client demande au serveur d’établir une connexion TLS. [1] L’un des principaux moyens d’y parvenir consiste à utiliser un numéro de port différent pour les connexions TLS. Par exemple, le port 80 est généralement utilisé pour le trafic HTTP non chiffré tandis que le port 443 est le port commun utilisé pour le trafic HTTPS chiffré. Un autre mécanisme consiste pour le client à faire une demande spécifique au protocole au serveur pour basculer la connexion vers TLS ; par exemple, en faisant une requête STARTTLS lors de l’utilisation des protocoles mail et news .
Une fois que le client et le serveur ont convenu d’utiliser TLS, ils négocient une connexion avec état en utilisant une procédure d’ établissement de liaison . [2] Les protocoles utilisent une poignée de main avec un chiffrement asymétrique pour établir non seulement les paramètres de chiffrement, mais également une clé partagée spécifique à la session avec laquelle la communication ultérieure est chiffrée à l’aide d’un chiffrement symétrique . Au cours de cette poignée de main, le client et le serveur s’accordent sur différents paramètres utilisés pour établir la sécurité de la connexion :
- La poignée de main commence lorsqu’un client se connecte à un serveur compatible TLS demandant une connexion sécurisée et que le client présente une liste des suites de chiffrement prises en charge ( chiffres et fonctions de hachage ).
- Dans cette liste, le serveur choisit une fonction de chiffrement et de hachage qu’il prend également en charge et informe le client de la décision.
- Le serveur fournit alors généralement une identification sous la forme d’un certificat numérique . Le certificat contient le nom du serveur , l’ autorité de certification (CA) de confiance qui garantit l’authenticité du certificat et la clé de cryptage publique du serveur.
- Le client confirme la validité du certificat avant de poursuivre.
- Pour générer les clés de session utilisées pour la connexion sécurisée, le client soit :
- chiffre un nombre aléatoire ( PreMasterSecret ) avec la clé publique du serveur et envoie le résultat au serveur (que seul le serveur doit pouvoir déchiffrer avec sa clé privée) ; les deux parties utilisent ensuite le nombre aléatoire pour générer une clé de session unique pour le chiffrement et le déchiffrement ultérieurs des données pendant la session
- utilise l’échange de clés Diffie-Hellman pour générer en toute sécurité une clé de session aléatoire et unique pour le chiffrement et le déchiffrement qui a la propriété supplémentaire de secret de transmission : si la clé privée du serveur est divulguée à l’avenir, elle ne peut pas être utilisée pour déchiffrer la session en cours, même si la session est interceptée et enregistrée par un tiers.
Ceci conclut la poignée de main et commence la connexion sécurisée, qui est chiffrée et déchiffrée avec la clé de session jusqu’à ce que la connexion se ferme. Si l’une des étapes ci-dessus échoue, la négociation TLS échoue et la connexion n’est pas créée.
TLS et SSL ne s’intègrent parfaitement dans aucune couche unique du modèle OSI ou du modèle TCP/IP . [3] [4] TLS s’exécute “au-dessus d’un protocole de transport fiable (par exemple, TCP)” [5] , ce qui impliquerait qu’il se trouve au-dessus de la couche de transport . Il sert de chiffrement aux couches supérieures, ce qui est normalement la fonction de la couche de présentation . Cependant, les applications utilisent généralement TLS comme s’il s’agissait d’une couche de transport, [3] [4] même si les applications utilisant TLS doivent contrôler activement l’initiation des poignées de main TLS et la gestion des certificats d’authentification échangés. [5]
Lorsqu’elles sont sécurisées par TLS, les connexions entre un client (par exemple, un navigateur Web) et un serveur (par exemple, wikipedia.org) doivent avoir une ou plusieurs des propriétés suivantes :
- La connexion est privée (ou sécurisée ) car un algorithme à clé symétrique est utilisé pour chiffrer les données transmises. Les clés de ce chiffrement symétrique sont générées de manière unique pour chaque connexion et sont basées sur un secret partagé qui a été négocié au début de la session. Le serveur et le client négocient les détails de l’algorithme de chiffrement et des clés cryptographiques à utiliser avant la transmission du premier octet de données (voir ci-dessous). La négociation d’un secret partagé est à la fois sécurisée (le secret négocié est inaccessible aux oreilles indiscrètes et ne peut être obtenu, même par un attaquant qui se place au milieu de la connexion) et fiable (aucun attaquant ne peut modifier les communications pendant la négociation sans être détecté).
- L’identité des parties communicantes peut être authentifiée à l’ aide de la cryptographie à clé publique . Cette authentification est obligatoire pour le serveur et facultative pour le client. [6]
- La connexion est fiable car chaque message transmis comprend une vérification de l’intégrité du message à l’aide d’un code d’authentification de message pour empêcher la perte ou l’altération non détectée des données pendant la transmission. [7] : 3
En plus de ce qui précède, une configuration minutieuse de TLS peut fournir des propriétés supplémentaires liées à la confidentialité, telles que le secret de transmission , garantissant que toute divulgation future de clés de chiffrement ne peut pas être utilisée pour déchiffrer des communications TLS enregistrées dans le passé.
TLS prend en charge de nombreuses méthodes différentes pour échanger des clés, chiffrer des données et authentifier l’intégrité des messages. Par conséquent, la configuration sécurisée de TLS implique de nombreux paramètres configurables, et tous les choix ne fournissent pas toutes les propriétés liées à la confidentialité décrites dans la liste ci-dessus (voir les tableaux ci-dessous § Échange de clé , § Sécurité du chiffrement et § Intégrité des données ).
Des tentatives ont été faites pour subvertir certains aspects de la sécurité des communications que TLS cherche à fournir, et le protocole a été révisé à plusieurs reprises pour faire face à ces menaces de sécurité. Les développeurs de navigateurs Web ont révisé à plusieurs reprises leurs produits pour se défendre contre les faiblesses de sécurité potentielles après leur découverte (voir l’historique de prise en charge TLS/SSL des navigateurs Web).
Histoire et développement
| Protocole | Publié | Statut |
|---|---|---|
| SSL 1.0 | Inédit | Inédit |
| SSL 2.0 | 1995 | Obsolète en 2011 ( RFC 6176 ) |
| SSL 3.0 | 1996 | Obsolète en 2015 ( RFC 7568 ) |
| TLS 1.0 | 1999 | Obsolète en 2021 ( RFC 8996 ) [8] [9] [10] |
| TLS 1.1 | 2006 | Obsolète en 2021 ( RFC 8996 ) [8] [9] [10] |
| TLS 1.2 | 2008 | |
| TLS 1.3 | 2018 |
Système de réseau de données sécurisé
Le protocole TLS (Transport Layer Security Protocol), ainsi que plusieurs autres plates-formes de sécurité réseau de base, ont été développés dans le cadre d’une initiative conjointe lancée en août 1986 entre la National Security Agency, le National Bureau of Standards, la Defense Communications Agency et douze communications et sociétés informatiques qui ont lancé un projet spécial appelé Secure Data Network System (SDNS). [11]Le programme a été décrit en septembre 1987 lors de la 10e Conférence nationale sur la sécurité informatique dans un ensemble complet d’articles publiés. Le programme de recherche innovant s’est concentré sur la conception de la prochaine génération de réseaux de communication informatique sécurisés et de spécifications de produits à mettre en œuvre pour des applications sur des internets publics et privés. Il était destiné à compléter les nouvelles normes Internet OSI qui émergent rapidement, à la fois dans les profils GOSIP du gouvernement américain et dans l’énorme effort Internet ITU-ISO JTC1 au niveau international. Connu à l’origine sous le nom de protocole SP4, il a été renommé TLS puis publié en 1995 en tant que norme internationale ITU-T X.274 | ISO/CEI 10736:1995.
Programmation réseau sécurisée
Les premiers efforts de recherche vers la sécurité de la couche de transport comprenaient l’ interface de programmation d’application (API) Secure Network Programming (SNP) , qui en 1993 a exploré l’approche d’avoir une API de couche de transport sécurisée ressemblant étroitement aux sockets Berkeley , pour faciliter la mise à niveau des applications réseau préexistantes avec la sécurité. mesures. [12]
SSL 1.0, 2.0 et 3.0
Netscape a développé les protocoles SSL originaux, et Taher Elgamal , scientifique en chef chez Netscape Communications de 1995 à 1998, a été décrit comme le “père de SSL”. [13] [14] [15] [16]SSL version 1.0 n’a jamais été rendu public en raison de graves failles de sécurité dans le protocole. La version 2.0, après sa sortie en février 1995, s’est rapidement révélée contenir un certain nombre de failles de sécurité et de convivialité. Il utilisait les mêmes clés cryptographiques pour l’authentification et le chiffrement des messages. Il avait une construction MAC faible qui utilisait la fonction de hachage MD5 avec un préfixe secret, le rendant vulnérable aux attaques d’extension de longueur. Et il n’offrait aucune protection ni pour la poignée de main d’ouverture ni pour la fermeture d’un message explicite, ce qui signifiait que les attaques de l’homme du milieu pouvaient passer inaperçues. De plus, SSL 2.0 supposait un service unique et un certificat de domaine fixe, en conflit avec la fonctionnalité largement utilisée d’hébergement virtuel dans les serveurs Web, de sorte que la plupart des sites Web étaient effectivement empêchés d’utiliser SSL.
Ces failles ont nécessité la refonte complète du protocole vers SSL version 3.0. [17] [15] Sorti en 1996, il a été produit par Paul Kocher travaillant avec les ingénieurs de Netscape Phil Karlton et Alan Freier, avec une implémentation de référence par Christopher Allen et Tim Dierks de Consensus Development. Les nouvelles versions de SSL/TLS sont basées sur SSL 3.0. Le projet de 1996 de SSL 3.0 a été publié par l’IETF en tant que document historique dans la RFC 6101 .
SSL 2.0 a été déprécié en 2011 par RFC 6176 . En 2014, SSL 3.0 s’est avéré vulnérable à l’ attaque POODLE qui affecte tous les chiffrements par blocs dans SSL ; RC4 , le seul chiffrement non-bloc pris en charge par SSL 3.0, est également vraisemblablement cassé tel qu’il est utilisé dans SSL 3.0. [18] SSL 3.0 a été déprécié en juin 2015 par la RFC 7568 .
TLS 1.0
TLS 1.0 a été défini pour la première fois dans la RFC 2246 en janvier 1999 comme une mise à niveau de SSL version 3.0 et écrit par Christopher Allen et Tim Dierks de Consensus Development. Comme indiqué dans la RFC, “les différences entre ce protocole et SSL 3.0 ne sont pas dramatiques, mais elles sont suffisamment importantes pour empêcher l’interopérabilité entre TLS 1.0 et SSL 3.0”. Tim Dierks a écrit plus tard que ces changements, et le changement de nom de “SSL” en “TLS”, étaient un geste pour sauver la face de Microsoft, “donc il ne semblerait pas que l’IETF ne fasse qu’approuver le protocole de Netscape”. [19]
Le Conseil PCI a suggéré que les organisations migrent de TLS 1.0 vers TLS 1.1 ou supérieur avant le 30 juin 2018. [20] [21] En octobre 2018, Apple , Google , Microsoft et Mozilla ont annoncé conjointement qu’ils rendraient obsolètes TLS 1.0 et 1.1 en mars. 2020. [8]
TLS 1.1
TLS 1.1 a été défini dans la RFC 4346 en avril 2006. [22] Il s’agit d’une mise à jour de TLS version 1.0. Les différences significatives dans cette version incluent :
- Protection supplémentaire contre les attaques par chaînage de blocs de chiffrement (CBC).
- Le vecteur d’initialisation implicite (IV) a été remplacé par un IV explicite.
- Modification de la gestion des erreurs de remplissage .
- Prise en charge de l’ enregistrement IANA des paramètres. [23] : 2
La prise en charge des versions 1.0 et 1.1 de TLS a été largement dépréciée par les sites Web vers 2020, désactivant l’accès aux versions de Firefox avant 24 et aux navigateurs basés sur Chromium avant 29. [24] [25] [26]
TLS 1.2
TLS 1.2 a été défini dans la RFC 5246 en août 2008. Il est basé sur la spécification TLS 1.1 antérieure. Les principales différences incluent :
- La combinaison MD5 – SHA-1 dans la fonction pseudo -aléatoire (PRF) a été remplacée par SHA-256 , avec une option pour utiliser les PRF spécifiées par la suite de chiffrement .
- La combinaison MD5–SHA-1 dans le hachage de message fini a été remplacée par SHA-256, avec une option pour utiliser des algorithmes de hachage spécifiques à la suite de chiffrement. Cependant, la taille du hachage dans le message fini doit toujours être d’au moins 96 bits . [27]
- La combinaison MD5–SHA-1 dans l’élément signé numériquement a été remplacée par un seul hachage négocié lors de la poignée de main , qui est par défaut SHA-1.
- Amélioration de la capacité du client et du serveur à spécifier les hachages et les algorithmes de signature qu’ils acceptent.
- Extension de la prise en charge des chiffrements de chiffrement authentifiés , utilisés principalement pour le mode Galois/Counter Mode (GCM) et le mode CCM du chiffrement Advanced Encryption Standard (AES).
- La définition des extensions TLS et les suites de chiffrement AES ont été ajoutées. [23] : 2
Toutes les versions de TLS ont été affinées dans la RFC 6176 en mars 2011, supprimant leur rétrocompatibilité avec SSL de sorte que les sessions TLS ne négocient jamais l’utilisation de la version 2.0 de Secure Sockets Layer (SSL).
TLS 1.3
TLS 1.3 a été défini dans la RFC 8446 en août 2018. Il est basé sur la spécification TLS 1.2 antérieure. Les principales différences par rapport à TLS 1.2 incluent : [28]
- Séparer les algorithmes d’accord de clé et d’authentification des suites de chiffrement
- Suppression de la prise en charge des courbes elliptiques nommées faibles et moins utilisées
- Suppression de la prise en charge des fonctions de hachage cryptographique MD5 et SHA-224
- Exiger des signatures numériques même lorsqu’une configuration précédente est utilisée
- Intégration de HKDF et de la proposition DH semi-éphémère
- Remplacement de la reprise par PSK et tickets
- Prise en charge des poignées de main 1- RTT et prise en charge initiale de 0- RTT
- Mandater le secret de transmission parfait , au moyen de l’utilisation de clés éphémères lors de l’accord de clé (EC) DH
- Suppression de la prise en charge de nombreuses fonctionnalités non sécurisées ou obsolètes, notamment la compression , la renégociation, les chiffrements non AEAD , l’échange de clés non PFS (parmi lesquels les échanges de clés RSA statiques et DH statiques ), les groupes DHE personnalisés , la négociation du format de point EC, le protocole Change Cipher Spec, Heure UNIX du message Hello et entrée AD du champ de longueur dans les chiffrements AEAD
- Interdire la négociation SSL ou RC4 pour la rétrocompatibilité
- Intégration de l’utilisation du hachage de session
- Dépréciation de l’utilisation du numéro de version de la couche d’enregistrement et gel du numéro pour une meilleure rétrocompatibilité
- Déplacer certains détails d’algorithme liés à la sécurité d’une annexe à la spécification et reléguer ClientKeyShare à une annexe
- Ajout du chiffrement de flux ChaCha20 avec le code d’authentification de message Poly1305
- Ajout des algorithmes de signature numérique Ed25519 et Ed448
- Ajout des protocoles d’échange de clés X25519 et X448
- Ajout de la prise en charge de l’envoi de plusieurs réponses OCSP
- Chiffrement de tous les messages de poignée de main après le ServerHello
Network Security Services (NSS), la bibliothèque de cryptographie développée par Mozilla et utilisée par son navigateur Web Firefox , a activé TLS 1.3 par défaut en février 2017. [29] La prise en charge de TLS 1.3 a ensuite été ajoutée — mais en raison de problèmes de compatibilité pour un petit nombre de utilisateurs, pas automatiquement activés [30] — à Firefox 52.0 , sorti en mars 2017. TLS 1.3 a été activé par défaut en mai 2018 avec la sortie de Firefox 60.0 . [31]
Google Chrome a défini TLS 1.3 comme version par défaut pendant une courte période en 2017. Il l’a ensuite supprimé par défaut, en raison de boîtiers de médiation incompatibles tels que les proxies Web Blue Coat . [32]
Lors de l’IETF 100 Hackathon , qui s’est déroulé à Singapour en 2017, le groupe TLS a travaillé sur l’adaptation d’applications open source pour utiliser TLS 1.3. [33] [34] Le groupe TLS était composé d’individus du Japon, du Royaume-Uni et de Maurice via l’équipe cyberstorm.mu. [34] Ce travail a été poursuivi dans le Hackathon IETF 101 à Londres , [35] et le Hackathon IETF 102 à Montréal. [36]
wolfSSL a permis l’utilisation de TLS 1.3 à partir de la version 3.11.1 , publiée en mai 2017 . ainsi que de nombreuses versions plus anciennes. Une série de blogs ont été publiés sur la différence de performances entre TLS 1.2 et 1.3. [39]
DansSeptembre 2018, le projet populaire OpenSSL a publié la version 1.1.1 de sa bibliothèque, dans laquelle la prise en charge de TLS 1.3 était “la nouvelle fonctionnalité phare”. [40]
La prise en charge de TLS 1.3 a été ajoutée pour la première fois à SChannel avec Windows 11 et Windows Server 2022 . [41]
Sécurité des transports d’entreprise
L’ Electronic Frontier Foundation a fait l’ éloge de TLS 1.3 et s’est dite préoccupée par la variante de protocole Enterprise Transport Security (ETS) qui désactive intentionnellement d’importantes mesures de sécurité dans TLS 1.3. [42] Initialement appelé Enterprise TLS (eTLS), ETS est une norme publiée connue sous le nom de « ETSI TS103523-3 », « Middlebox Security Protocol, Part3 : Enterprise Transport Security ». Il est destiné à être utilisé entièrement dans des réseaux propriétaires tels que des systèmes bancaires. ETS ne prend pas en charge la confidentialité persistante afin de permettre aux organisations tierces connectées aux réseaux propriétaires de pouvoir utiliser leur clé privée pour surveiller le trafic réseau afin de détecter les logiciels malveillants et de faciliter la réalisation d’audits. [43] [44]Malgré les avantages revendiqués, l’EFF a averti que la perte du secret de transmission pourrait faciliter l’exposition des données tout en affirmant qu’il existe de meilleures façons d’analyser le trafic.
Certificats numériques
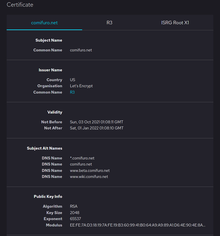
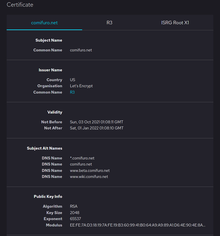 Exemple de site web avec certificat numérique
Exemple de site web avec certificat numérique
Un certificat numérique certifie la propriété d’une clé publique par le sujet nommé du certificat et indique certaines utilisations attendues de cette clé. Cela permet à d’autres (parties utilisatrices) de s’appuyer sur des signatures ou sur des affirmations faites par la clé privée qui correspond à la clé publique certifiée. Les magasins de clés et les magasins de confiance peuvent être dans différents formats, tels que .pem, .crt, .pfx et .jks.
Autorités de certification
TLS s’appuie généralement sur un ensemble d’autorités de certification tierces de confiance pour établir l’authenticité des certificats. La confiance est généralement ancrée dans une liste de certificats distribués avec un logiciel d’agent utilisateur [45] et peut être modifiée par la partie utilisatrice.
Selon Netcraft , qui surveille les certificats TLS actifs, l’autorité de certification (CA) leader du marché est Symantec depuis le début de leur enquête (ou VeriSign avant que l’unité commerciale des services d’authentification ne soit achetée par Symantec). En 2015, Symantec représentait un peu moins d’un tiers de tous les certificats et 44 % des certificats valides utilisés par les 1 million de sites Web les plus fréquentés, selon Netcraft. [46] En 2017, Symantec a vendu son activité TLS/SSL à DigiCert. [47] Dans un rapport mis à jour, il a été montré qu’IdenTrust , DigiCert et Sectigo sont les 3 principales autorités de certification en termes de part de marché depuis mai 2019.[48]
En conséquence du choix des certificats X.509 , des autorités de certification et une infrastructure à clé publique sont nécessaires pour vérifier la relation entre un certificat et son propriétaire, ainsi que pour générer, signer et administrer la validité des certificats. Bien que cela puisse être plus pratique que de vérifier les identités via un réseau de confiance , les divulgations de surveillance de masse de 2013 ont fait savoir plus largement que les autorités de certification sont un point faible du point de vue de la sécurité, permettant des attaques de l’homme du milieu (MITM) si l’autorité de certification coopère (ou est compromise). [49] [50]
Algorithmes
Échange de clé ou accord de clé
Avant qu’un client et un serveur puissent commencer à échanger des informations protégées par TLS, ils doivent échanger ou convenir en toute sécurité d’une clé de chiffrement et d’un chiffrement à utiliser lors du chiffrement des données (voir § Chiffrement ). Parmi les méthodes utilisées pour l’échange/l’accord de clés figurent : les clés publiques et privées générées avec RSA (notées TLS_RSA dans le protocole de prise de contact TLS), Diffie–Hellman (TLS_DH), Diffie–Hellman éphémère (TLS_DHE), Diffie–Hellman à courbe elliptique ( TLS_ECDH), Diffie–Hellman à courbe elliptique éphémère (TLS_ECDHE), Diffie–Hellman anonyme (TLS_DH_anon), [7] clé pré-partagée (TLS_PSK) [51] et Secure Remote Password (TLS_SRP). [52]
Les méthodes d’accord de clé TLS_DH_anon et TLS_ECDH_anon n’authentifient pas le serveur ou l’utilisateur et sont donc rarement utilisées car elles sont vulnérables aux attaques de type ” man-in-the-middle” . Seuls TLS_DHE et TLS_ECDHE fournissent le secret de transmission .
Les certificats de clé publique utilisés pendant l’échange/l’accord varient également dans la taille des clés de chiffrement publiques/privées utilisées pendant l’échange et donc la robustesse de la sécurité fournie. En juillet 2013, Google a annoncé qu’il n’utiliserait plus de clés publiques de 1024 bits et passerait à la place à des clés de 2048 bits pour augmenter la sécurité du cryptage TLS qu’il fournit à ses utilisateurs car la force de cryptage est directement liée à la taille de la clé. . [53] [54]
| Algorithme | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | Statut |
|---|---|---|---|---|---|---|---|
| RSA | Oui | Oui | Oui | Oui | Oui | Non | Défini pour TLS 1.2 dans les RFC |
| DH – RSA | Non | Oui | Oui | Oui | Oui | Non | |
| DHE – RSA ( secret de transmission ) | Non | Oui | Oui | Oui | Oui | Oui | |
| ECDH – RSA | Non | Non | Oui | Oui | Oui | Non | |
| ECDHE – RSA (secret transmis) | Non | Non | Oui | Oui | Oui | Oui | |
| DH – DSS | Non | Oui | Oui | Oui | Oui | Non | |
| DHE – DSS (secret de transmission) | Non | Oui | Oui | Oui | Oui | Non [55] | |
| ECDH – ECDSA | Non | Non | Oui | Oui | Oui | Non | |
| ECDHE – ECDSA (secret transmis) | Non | Non | Oui | Oui | Oui | Oui | |
| ECDH – EdDSA | Non | Non | Oui | Oui | Oui | Non | |
| ECDHE – EdDSA (secret transmis) [56] | Non | Non | Oui | Oui | Oui | Oui | |
| PSK | Non | Non | Oui | Oui | Oui | ||
| PSK – RSA | Non | Non | Oui | Oui | Oui | ||
| DHE – PSK (secret de transmission) | Non | Non | Oui | Oui | Oui | Oui | |
| ECDHE – PSK (secret transmis) | Non | Non | Oui | Oui | Oui | Oui | |
| PRS | Non | Non | Oui | Oui | Oui | ||
| SRP – DSS | Non | Non | Oui | Oui | Oui | ||
| SRP – RSA | Non | Non | Oui | Oui | Oui | ||
| KerberosName | Non | Non | Oui | Oui | Oui | ||
| DH -ANON (non sécurisé) | Non | Oui | Oui | Oui | Oui | ||
| ECDH -ANON (non sécurisé) | Non | Non | Oui | Oui | Oui | ||
| GOST R 34.10-94 / 34.10-2001 [57] | Non | Non | Oui | Oui | Oui | Proposé dans les brouillons RFC |
Chiffrer
| Chiffrer | Version du protocole | Statut | |||||||
|---|---|---|---|---|---|---|---|---|---|
| Taper | Algorithme | Force nominale (bits) | SSL 2.0 | SSL 3.0 [n 1] [n 2] [n 3] [n 4] |
TLS 1.0 [n 1] [n 3] |
TLS 1.1 [n 1] |
TLS 1.2 [n 1] |
TLS 1.3 | |
| Chiffrement par bloc avec mode de fonctionnement |
MCG AES [58] [n 5] | 256, 128 | N / A | N / A | N / A | N / A | Sécurise | Sécurise | Défini pour TLS 1.2 dans les RFC |
| AES CCM [59] [n 5] | N / A | N / A | N / A | N / A | Sécurise | Sécurise | |||
| AES SRC [n 6] | N / A | Précaire | Dépend des atténuations | Dépend des atténuations | Dépend des atténuations | N / A | |||
| Camélia GCM [60] [n 5] | 256, 128 | N / A | N / A | N / A | N / A | Sécurise | N / A | ||
| Camélia CBC [61] [n 6] | N / A | Précaire | Dépend des atténuations | Dépend des atténuations | Dépend des atténuations | N / A | |||
| MCG ARIA [62] [n 5] | 256, 128 | N / A | N / A | N / A | N / A | Sécurise | N / A | ||
| ARIA CBC [62] [n 6] | N / A | N / A | Dépend des atténuations | Dépend des atténuations | Dépend des atténuations | N / A | |||
| SEED CTF [63] [n 6] | 128 | N / A | Précaire | Dépend des atténuations | Dépend des atténuations | Dépend des atténuations | N / A | ||
| 3DES EDE CBC [n 6] [n 7] | 112 [n 8] | Précaire | Précaire | Précaire | Précaire | Précaire | N / A | ||
| GOST 28147-89 CNT [57] [n 7] | 256 | N / A | N / A | Précaire | Précaire | Précaire | N / A | Défini dans la RFC 4357 | |
| IDÉE CBC [n 6] [n 7] [n 9] | 128 | Précaire | Précaire | Précaire | Précaire | N / A | N / A | Supprimé de TLS 1.2 | |
| DES CBC [n 6] [n 7] [n 9] | 0 56 | Précaire | Précaire | Précaire | Précaire | N / A | N / A | ||
| 0 40 [n 10] | Précaire | Précaire | Précaire | N / A | N / A | N / A | Interdit dans TLS 1.1 et versions ultérieures | ||
| RC2 SRC [n 6] [n 7] | 0 40 [n 10] | Précaire | Précaire | Précaire | N / A | N / A | N / A | ||
| Chiffrement de flux | ChaCha20 – Poly1305 [68] [n 5] | 256 | N / A | N / A | N / A | N / A | Sécurise | Sécurise | Défini pour TLS 1.2 dans les RFC |
| RC4 [n 11] | 128 | Précaire | Précaire | Précaire | Précaire | Précaire | N / A | Interdit dans toutes les versions de TLS par RFC 7465 | |
| 0 40 [n 10] | Précaire | Précaire | Précaire | N / A | N / A | N / A | |||
| Rien | Nul [n 12] | – | Précaire | Précaire | Précaire | Précaire | Précaire | N / A | Défini pour TLS 1.2 dans les RFC |
Remarques
- ^ a b c d RFC 5746 doit être implémenté pour corriger un défaut de renégociation qui autrement casserait ce protocole.
- ^ Si les bibliothèques implémentent les correctifs répertoriés dans RFC 5746 , cela viole la spécification SSL 3.0, que l’IETF ne peut pas modifier contrairement à TLS. La plupart des bibliothèques actuelles implémentent le correctif et ignorent la violation qui en résulte.
- ^ a b L’ attaque BEAST brise tous les chiffrements par blocs (chiffres CBC) utilisés dans SSL 3.0 et TLS 1.0 à moins qu’ils ne soient atténués par le client et/ou le serveur. Voir § Navigateurs Web .
- ^ L’ attaque POODLE brise tous les chiffrements par blocs (chiffres CBC) utilisés dans SSL 3.0 à moins qu’ils ne soient atténués par le client et/ou le serveur. Voir § Navigateurs Web .
- ^ a b c d e Les chiffrements AEAD (tels que GCM et CCM ) ne peuvent être utilisés que dans TLS 1.2 ou version ultérieure.
- ^ a b c d e f g h Les chiffrements CBC peuvent être attaqués avec l’ attaque Lucky Thirteen si la bibliothèque n’est pas écrite avec soin pour éliminer les canaux latéraux de synchronisation.
- ^ a b c d e L’ attaque Sweet32 brise les chiffrements par bloc avec une taille de bloc de 64 bits. [64]
- ^ Bien que la longueur de clé de 3DES soit de 168 bits, la force de sécurité effective de 3DES n’est que de 112 bits, [65] ce qui est inférieur au minimum recommandé de 128 bits. [66]
- ^ a b IDEA et DES ont été supprimés de TLS 1.2. [67]
- ^ a b c Des suites de chiffrement de 40 bits ont été intentionnellement conçues avec des longueurs de clé réduites pour se conformer aux réglementations américaines annulées depuis interdisant l’exportation de logiciels cryptographiques contenant certains algorithmes de chiffrement puissants (voir Exportation de cryptographie des États-Unis ). Ces suites faibles sont interdites dans TLS 1.1 et versions ultérieures.
- ^ L’utilisation de RC4 dans toutes les versions de TLS est interdite par la RFC 7465 (car les attaques RC4 affaiblissent ou cassent RC4 utilisé dans SSL/TLS).
- ^ Authentification uniquement, pas de cryptage.
Intégrité des données
Un code d’authentification de message (MAC) est utilisé pour l’intégrité des données. HMAC est utilisé pour le mode CBC des chiffrements par blocs. Le chiffrement authentifié (AEAD) tel que le mode GCM et le mode CCM utilise le MAC intégré à AEAD et n’utilise pas le HMAC . [69] PRF basé sur HMAC ou HKDF est utilisé pour la prise de contact TLS.
| Algorithme | SSL 2.0 | SSL 3.0 | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 | Statut |
|---|---|---|---|---|---|---|---|
| HMAC – MD5 | Oui | Oui | Oui | Oui | Oui | Non | Défini pour TLS 1.2 dans les RFC |
| HMAC – SHA1 | Non | Oui | Oui | Oui | Oui | Non | |
| HMAC – SHA256/384 | Non | Non | Non | Non | Oui | Non | |
| AEAD | Non | Non | Non | Non | Oui | Oui | |
| GOST 28147-89 IMIT [57] | Non | Non | Oui | Oui | Oui | Proposé dans les brouillons RFC | |
| GOST R 34.11-94 [57] | Non | Non | Oui | Oui | Oui |
Candidatures et adoption
Dans la conception d’applications, TLS est généralement implémenté au-dessus des protocoles de la couche de transport, cryptant toutes les données liées au protocole de protocoles tels que HTTP , FTP , SMTP , NNTP et XMPP .
Historiquement, TLS a été utilisé principalement avec des protocoles de transport fiables tels que le protocole TCP ( Transmission Control Protocol ). Cependant, il a également été implémenté avec des protocoles de transport orientés datagramme, tels que le protocole de datagramme utilisateur (UDP) et le protocole de contrôle de congestion de datagramme (DCCP), dont l’utilisation a été normalisée indépendamment en utilisant le terme Datagram Transport Layer Security (DTLS) .
Sites Internet
L’une des principales utilisations de TLS consiste à sécuriser le trafic World Wide Web entre un site Web et un navigateur Web codé avec le protocole HTTP. Cette utilisation de TLS pour sécuriser le trafic HTTP constitue le protocole HTTPS . [70]
| Version du protocole | Prise en charge du site Web [71] | Sécurité [71] [72] |
|---|---|---|
| SSL 2.0 | 0,4 % | Précaire |
| SSL 3.0 | 3,0 % | Insécurisé [73] |
| TLS 1.0 | 43,8 % | Obsolète [8] [9] [10] |
| TLS 1.1 | 47,8 % | Obsolète [8] [9] [10] |
| TLS 1.2 | 99,6 % | Dépend du chiffrement [n 1] et des atténuations du client [n 2] |
| TLS 1.3 | 49,7 % | Sécurise |
Remarques
- ^ voir § Table de chiffrement ci-dessus
- ^ voir § Navigateurs Web etsections TLS/SSL
Navigateurs Web
Depuis avril 2016 [update], les dernières versions de tous les principaux navigateurs Web prennent en charge TLS 1.0, 1.1 et 1.2, et les ont activés par défaut. Cependant, tous les systèmes d’exploitation Microsoft pris en charge ne prennent pas en charge la dernière version d’IE. De plus, de nombreux systèmes d’exploitation Microsoft prennent actuellement en charge plusieurs versions d’IE, mais cela a changé selon la FAQ sur la politique de cycle de vie de la prise en charge d’Internet Explorer de Microsoft., “à compter du 12 janvier 2016, seule la version la plus récente d’Internet Explorer disponible pour un système d’exploitation pris en charge recevra une assistance technique et des mises à jour de sécurité.” La page continue ensuite en répertoriant la dernière version prise en charge d’IE à cette date pour chaque système d’exploitation. La prochaine date critique serait le moment où un système d’exploitation atteint la fin de la phase de vie, qui figure dans la fiche d’information sur le cycle de vie de Windows de Microsoft .
Les atténuations contre les attaques connues ne suffisent pas encore :
- Atténuations contre l’attaque POODLE : certains navigateurs empêchent déjà le repli vers SSL 3.0 ; cependant, cette atténuation doit être prise en charge non seulement par les clients, mais également par les serveurs. La désactivation de SSL 3.0 lui-même, la mise en œuvre du “fractionnement d’enregistrements anti-POODLE” ou le refus des chiffrements CBC dans SSL 3.0 sont nécessaires.
- Google Chrome : complet (TLS_FALLBACK_SCSV est implémenté depuis la version 33, le retour à SSL 3.0 est désactivé depuis la version 39, SSL 3.0 lui-même est désactivé par défaut depuis la version 40. Le support de SSL 3.0 lui-même a été abandonné depuis la version 44.)
- Mozilla Firefox : complet (le support de SSL 3.0 lui-même est abandonné depuis la version 39 . SSL 3.0 lui-même est désactivé par défaut et les retours vers SSL 3.0 sont désactivés depuis la version 34 , TLS_FALLBACK_SCSV est implémenté depuis la version 35. Dans ESR, SSL 3.0 lui-même est désactivé par par défaut et TLS_FALLBACK_SCSV est implémenté depuis ESR 31.3.)
- Internet Explorer : partiel (uniquement dans la version 11, SSL 3.0 est désactivé par défaut depuis avril 2015. Les versions 10 et antérieures sont toujours vulnérables contre POODLE.)
- Opera : complet (TLS_FALLBACK_SCSV est implémenté depuis la version 20, “anti-POODLE record splitting”, qui n’est efficace qu’avec l’implémentation côté client, est implémenté depuis la version 25, SSL 3.0 lui-même est désactivé par défaut depuis la version 27. Support de SSL 3.0 lui-même sera abandonné depuis la version 31.)
- Safari : complet (uniquement sur OS X 10.8 et versions ultérieures et iOS 8, les chiffrements CBC lors du retour à SSL 3.0 sont refusés, mais cela signifie qu’il utilisera RC4, ce qui n’est pas non plus recommandé. La prise en charge de SSL 3.0 lui-même est abandonnée sur OS X 10.11 et versions ultérieures et iOS 9.)
- Atténuation contre les attaques RC4 :
- Google Chrome a désactivé RC4 sauf en tant que solution de secours depuis la version 43. RC4 est désactivé depuis Chrome 48.
- Firefox a désactivé RC4 sauf en tant que solution de secours depuis la version 36. Firefox 44 a désactivé RC4 par défaut.
- Opera a désactivé RC4 sauf en tant que solution de secours depuis la version 30. RC4 est désactivé depuis Opera 35.
- Internet Explorer pour Windows 7 / Server 2008 R2 et pour Windows 8 / Server 2012 a défini la priorité de RC4 sur la plus basse et peut également désactiver RC4, sauf en tant que solution de secours via les paramètres de registre. Internet Explorer 11 Mobile 11 pour Windows Phone 8.1 désactive RC4 sauf comme solution de secours si aucun autre algorithme activé ne fonctionne. Edge et IE 11 désactivent complètement RC4 en août 2016.
- Atténuation contre l’attaque FREAK :
- Le navigateur Android inclus avec Android 4.0 et les versions antérieures est toujours vulnérable à l’attaque FREAK.
- Internet Explorer 11 Mobile est toujours vulnérable à l’attaque FREAK.
- Google Chrome, Internet Explorer (ordinateur de bureau), Safari (ordinateur de bureau et mobile) et Opera (mobile) ont mis en place des mesures d’atténuation FREAK.
- Mozilla Firefox sur toutes les plateformes et Google Chrome sur Windows n’ont pas été affectés par FREAK.
| Navigateur | Version | Plateformes | Protocoles SSL | Protocoles TLS | Prise en charge des certificats | Vulnérabilités corrigées [n 1] | Sélection du protocole par l’utilisateur [n 2] |
||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | EV [n 3] [74] |
SHA-2 [75] |
ECDSA [76] |
BÊTE [n 4] | CRIMINALITÉ [n 5] | CANICHE (SSLv3) [n 6] | RC4 [n 7] | FRÉQUENCE [77] [78] | Embâcle | |||||
| Google Chrome ( Chrome pour Android ) [n 8] [n 9] |
1–9 | Windows (7+) macOS (10.11+) Linux Android (5.0+) iOS (12.2+) Chrome OS |
Désactivé par défaut | Activé par défaut | Oui | Non | Non | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Non affecté [83] |
Vulnérable (HTTPS) |
Vulnérable | Vulnérable | Vulnérable (sauf Windows) |
Vulnérable | Oui [n 10] | |
| 10–20 | Non [84] | Activé par défaut | Oui | Non | Non | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Vulnérable (HTTPS/SPDY) |
Vulnérable | Vulnérable | Vulnérable (sauf Windows) |
Vulnérable | Oui [n 10] | |||
| 21 | Non | Activé par défaut | Oui | Non | Non | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué [85] |
Vulnérable | Vulnérable | Vulnérable (sauf Windows) |
Vulnérable | Oui [n 10] | |||
| 22–29 | Non | Activé par défaut | Oui | Oui [86] | Non [86] [87] [88] [89] | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Vulnérable | Vulnérable | Vulnérable (sauf Windows) |
Vulnérable | Temporaire [n 11] |
|||
| 30–32 | Non | Activé par défaut | Oui | Oui | Oui [87] [88] [89] | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Vulnérable | Vulnérable | Vulnérable (sauf Windows) |
Vulnérable | Temporaire [n 11] |
|||
| 33–37 | Non | Activé par défaut | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
nécessite un système d’exploitation compatible SHA-2 [75] | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Partiellement atténué [n 12] |
Priorité la plus basse [92] [93] [94] |
Vulnérable (sauf Windows) |
Vulnérable | Temporaire [n 11] |
|||
| 38, 39 | Non | Activé par défaut | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Partiellement atténué | Priorité la plus basse | Vulnérable (sauf Windows) |
Vulnérable | Temporaire [n 11] |
|||
| 40 | Non | Désactivé par défaut [91] [95] | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Atténué [n 13] |
Priorité la plus basse | Vulnérable (sauf Windows) |
Vulnérable | Oui [n 14] | |||
| 41, 42 | Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Atténué | Priorité la plus basse | Atténué | Vulnérable | Oui [n 14] | |||
| 43 | Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Atténué | Uniquement comme solution de repli [n 15] [96] |
Atténué | Vulnérable | Oui [n 14] | |||
| 44–47 | Non | Non [97] | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Pas affecté | Uniquement comme repli [n 15] |
Atténué | Atténué [98] | Temporaire [n 11] |
|||
| 48, 49 | Non | Non | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | nécessite un système d’exploitation compatible ECC [76] | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 50–53 | Non | Non | Oui | Oui | Oui | Non | Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 54–66 | Non | Non | Oui | Oui | Oui | Désactivé par défaut (version brouillon) |
Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 67–69 | Non | Non | Oui | Oui | Oui | Oui (version préliminaire) |
Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 70–83 | Non | Non | Oui | Oui | Oui | Oui | Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 84–90 | Non | Non | Avertir par défaut | Avertir par défaut | Oui | Oui | Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| 91–99 | Non | Non | Non [101] | Non [101] | Oui | Oui | Oui (ordinateur de bureau uniquement) |
Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [99] [100] | Atténué | Atténué | Temporaire [n 11] |
|||
| ESC 100 | 101 | ||||||||||||||||||
| Navigateur | Version | Plateformes | SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | Certificat VE | Certificat SHA-2 | Certificat ECDSA | LA BÊTE | LA CRIMINALITÉ | CANICHE (SSLv3) | RC4 | MONSTRE | Embâcle | Sélection du protocole par l’utilisateur | |
| Microsoft Edge (basé sur Chromium) indépendant du système d’exploitation |
79–83 | Windows (7+) macOS (10.12+) Linux Android (4.4+) iOS (11.0+) |
Non | Non | Oui | Oui | Oui | Oui | Oui | Oui | Oui | Atténué | Pas affecté | Pas affecté | Désactivé par défaut | Atténué | Atténué | Oui [n 10] | |
| 84–90 | Non | Non | Avertir par défaut | Avertir par défaut | Oui | Oui | Oui | Oui | Oui | Atténué | Pas affecté | Pas affecté | Désactivé par défaut | Atténué | Atténué | Oui [n 10] | |||
| 91-99 | Non | Non | Non [102] | Non [102] | Oui | Oui | Oui | Oui | Oui | Atténué | Pas affecté | Pas affecté | Désactivé par défaut | Atténué | Atténué | Oui [n 10] | |||
| ESC 100 | 101 | ||||||||||||||||||
| Navigateur | Version | Plateformes | SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | Certificat VE | Certificat SHA-2 | Certificat ECDSA | LA BÊTE | LA CRIMINALITÉ | CANICHE (SSLv3) | RC4 | MONSTRE | Embâcle | Sélection du protocole par l’utilisateur | |
| Mozilla Firefox ( Firefox pour mobile ) [n 17] |
1.0, 1.5 | Windows (7+) macOS (10.12+) Linux Android (5.0+) iOS (11.4+) Firefox OS Maemo ESR uniquement pour : Windows (7+) macOS (10.12+) Linux |
Activé par défaut [103] |
Activé par défaut [103] |
Oui [103] | Non | Non | Non | Non | Oui [75] | Non | Non affecté [104] |
Pas affecté | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |
| 2 | Désactivé par défaut [103] [105] |
Activé par défaut | Oui | Non | Non | Non | Non | Oui | Oui [76] | Pas affecté | Pas affecté | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |||
| 3–7 | Désactivé par défaut | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui | Pas affecté | Pas affecté | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |||
| 8–10 RSE 10 |
Non [105] | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui | Pas affecté | Pas affecté | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |||
| 11–14 | Non | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui | Pas affecté | Vulnérable (SPDY) [85] |
Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |||
| 15–22 RSE 17.0–17.0.10 |
Non | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 10] | |||
| RSE 17.0.11 | Non | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Priorité la plus basse [106] [107] |
Pas affecté | Vulnérable | Oui [n 10] | |||
| 23 | Non | Activé par défaut | Oui | Désactivé par défaut [108] |
Non | Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 18] | |||
| 24, 25.0.0 RSE 24.0–24.1.0 |
Non | Activé par défaut | Oui | Désactivé par défaut | Désactivé par défaut [109] |
Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Vulnérable | Pas affecté | Vulnérable | Oui [n 18] | |||
| 25.0.1, 26 ESR 24.1.1 |
Non | Activé par défaut | Oui | Désactivé par défaut | Désactivé par défaut | Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Priorité la plus basse [106] [107] |
Pas affecté | Vulnérable | Oui [n 18] | |||
| 27–33 RSE 31.0–31.2 |
Non | Activé par défaut | Oui | Oui [110] [111] | Oui [112] [111] | Non | Oui | Oui | Oui | Pas affecté | Atténué | Vulnérable | Priorité la plus basse | Pas affecté | Vulnérable | Oui [n 18] | |||
| 34, 35 ESR 31.3–31.7 |
Non | Désactivé par défaut [113] [114] |
Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Atténué [n 19] |
Priorité la plus basse | Pas affecté | Vulnérable | Oui [n 18] | |||
| RSE 31.8 | Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Atténué | Priorité la plus basse | Pas affecté | Atténué [117] | Oui [n 18] | |||
| 36–38 RSE 38,0 |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Atténué | Uniquement comme repli [n 15] [118] |
Pas affecté | Vulnérable | Oui [n 18] | |||
| RSE 38.1–38.8 | Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Atténué | Uniquement comme repli [n 15] |
Pas affecté | Atténué [117] | Oui [n 18] | |||
| 39–43 | Non | Non [119] | Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Uniquement comme repli [n 15] |
Pas affecté | Atténué [117] | Oui [n 18] | |||
| 44–48 RSE 45 |
Non | Non | Oui | Oui | Oui | Non | Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] [120] [121] [122] [123] | Pas affecté | Atténué | Oui [n 18] | |||
| 49–59 RSE 52 |
Non | Non | Oui | Oui | Oui | Désactivé par défaut (version brouillon) [124] |
Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] | Pas affecté | Atténué | Oui [n 18] | |||
| 60–62 RSE 60 |
Non | Non | Oui | Oui | Oui | Oui (version préliminaire) |
Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] | Pas affecté | Atténué | Oui [n 18] | |||
| 63–77 RSE 68 |
Non | Non | Oui | Oui | Oui | Oui | Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] | Pas affecté | Atténué | Oui [n 18] | |||
| 78–99 RSE 78 RSE 91,0–91,8 |
Non | Non | Désactivé par défaut [125] | Désactivé par défaut [125] | Oui | Oui | Oui | Oui | Oui | Pas affecté | Atténué | Pas affecté | Désactivé par défaut [n 16] | Pas affecté | Atténué | Oui [n 18] | |||
| RSE 91.9 | 100 | ||||||||||||||||||
| Navigateur | Version | Plateformes | SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | Certificat VE | Certificat SHA-2 | Certificat ECDSA | LA BÊTE | LA CRIMINALITÉ | CANICHE (SSLv3) | RC4 | MONSTRE | Embâcle | Sélection du protocole par l’utilisateur | |
| Microsoft Internet Explorer (1–10) [n 20] |
1 fois | Windows 3.1 , 95 , NT , [n 21] [n 22] Mac OS 7 , 8 |
Pas de prise en charge SSL/TLS | ||||||||||||||||
| 2 | Oui | Non | Non | Non | Non | Non | Non | Non | Non | Pas de prise en charge SSL 3.0 ou TLS | Vulnérable | Vulnérable | Vulnérable | N / A | |||||
| 3 | Oui | Oui [128] | Non | Non | Non | Non | Non | Non | Non | Vulnérable | Pas affecté | Vulnérable | Vulnérable | Vulnérable | Vulnérable | Inconnue | |||
| 4 , 5 , 6 | Windows 3.1 , 95 , 98 , NT , 2000 [n 21] [n 22] Mac OS 7.1 , 8 , X , Solaris , HP-UX |
Activé par défaut | Activé par défaut | Désactivé par défaut [128] |
Non | Non | Non | Non | Non | Non | Vulnérable | Pas affecté | Vulnérable | Vulnérable | Vulnérable | Vulnérable | Oui [n 10] | ||
| 6 | Windows XP [n 22] | Activé par défaut | Activé par défaut | Désactivé par défaut | Non | Non | Non | Non | Oui (depuis SP3) [n 23] [129] |
Non | Atténué | Pas affecté | Vulnérable | Vulnérable | Vulnérable | Vulnérable | Oui [n 10] | ||
| 7 , 8 | Désactivé par défaut [130] |
Activé par défaut | Oui [130] | Non | Non | Non | Oui | Oui (depuis SP3) [n 23] [129] |
Non | Atténué | Pas affecté | Vulnérable | Vulnérable | Vulnérable | Vulnérable | Oui [n 10] | |||
| 6 | Serveur 2003 [n 22] | Activé par défaut | Activé par défaut | Désactivé par défaut | Non | Non | Non | Non | Oui (KB938397+KB968730) [n 23] [129] |
Non | Atténué | Pas affecté | Vulnérable | Vulnérable | Atténué [133] |
Atténué [134] |
Oui [n 10] | ||
| 7 , 8 | Désactivé par défaut [130] |
Activé par défaut | Oui [130] | Non | Non | Non | Oui | Oui (KB938397+KB968730) [n 23] [129] |
Non | Atténué | Pas affecté | Vulnérable | Vulnérable | Atténué [133] |
Atténué [134] |
Oui [n 10] | |||
| 7 , 8 , 9 | Windows Vista | Désactivé par défaut | Activé par défaut | Oui | Non | Non | Non | Oui | Oui | Oui [76] | Atténué | Pas affecté | Vulnérable | Vulnérable | Atténué [133] |
Atténué [134] |
Oui [n 10] | ||
| 7 , 8 , 9 | Serveur 2008 | Désactivé par défaut | Activé par défaut | Oui | Désactivé par défaut [135] (KB4019276) |
Désactivé par défaut [135] (KB4019276) |
Non | Oui | Oui | Oui [76] | Atténué | Pas affecté | Vulnérable | Vulnérable | Atténué [133] |
Atténué [134] |
Oui [n 10] | ||
| 8 , 9 , 10 | Windows 7/8 Serveur 2008 R2 / 2012 _ | Désactivé par défaut | Activé par défaut | Oui | Désactivé par défaut [136] |
Désactivé par défaut [136] |
Non | Oui | Oui | Oui | Atténué | Pas affecté | Vulnérable | Priorité la plus basse [137] [n 24] |
Atténué [133] |
Atténué [134] |
Oui [n 10] | ||
| Internet Explorer 11 [n 20] |
11 | Windows 7 Serveur 2008 R2 |
Désactivé par défaut | Désactivé par défaut [n 25] |
Oui | Oui [139] | Oui [139] | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué [n 25] |
Désactivé par défaut [143] | Atténué [133] |
Atténué [134] |
Oui [n 10] | |
| 11 [144] | Windows 8.1 | Désactivé par défaut | Désactivé par défaut [n 25] |
Oui | Oui [139] | Oui [139] | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué [n 25] |
Désactivé par défaut [n 16] | Atténué [133] |
Atténué [134] |
Oui [n 10] | ||
| Serveur 2012 Serveur 2012 R2 |
|||||||||||||||||||
| Navigateur | Version | Plateformes | SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | Certificat VE | Certificat SHA-2 | Certificat ECDSA | LA BÊTE | LA CRIMINALITÉ | CANICHE (SSLv3) | RC4 | MONSTRE | Embâcle | Sélection du protocole par l’utilisateur | |
| Microsoft Edge (12–18) (basé sur EdgeHTML) Client uniquement Internet Explorer 11 [n 20] |
11 | 12–13 | Windows 10 1507–1511 |
Désactivé par défaut | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] |
| 11 | 14–18 (client uniquement) |
Windows 10 1607–2004 Windows Serveur (SAC) 1709–2004 |
Non [145] | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | |
| Internet Explorer 11 [n 20] |
11 | Windows 10 20H2 Windows Serveur (SAC) 20H2 |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | |
| 11 | Windows 10 21H1 |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows 10 21H2 |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows 11 | Non | Désactivé par défaut | Oui | Oui | Oui | Oui [146] | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| Internet Explorer 11 [n 20] Versions LTSC |
11 | Windows 10 LTSB 2015 (1507) |
Désactivé par défaut | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | |
| 11 | Windows 10 LTSB 2016 (1607) |
Non [145] | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows Server 2016 (LTSB / 1607) |
Non [145] | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows 10 LTSC 2019 (1809) Windows Server 2019 (LTSC / 1809) |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows 10 LTSC 2021 (21H2) |
Non | Désactivé par défaut | Oui | Oui | Oui | Non | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| 11 | Windows Server 2022 (LTSC) |
Non | Désactivé par défaut | Oui | Oui | Oui | Oui [146] | Oui | Oui | Oui | Atténué | Pas affecté | Atténué | Désactivé par défaut [n 16] | Atténué | Atténué | Oui [n 10] | ||
| Navigateur | Version | Plateformes | SSL 2.0 (non sécurisé) | SSL 3.0 (non sécurisé) | TLS 1.0 (obsolète) | TLS 1.1 (obsolète) | TLS 1.2 | TLS 1.3 | Certificat VE | Certificat SHA-2 | Certificat ECDSA | LA BÊTE | LA CRIMINALITÉ | CANICHE (SSLv3) | RC4 | MONSTRE | Embâcle | Sélection du protocole par l’utilisateur | |
| Microsoft Internet Explorer Mobile [n 20] |
7, 9 | Windows Phone 7, 7.5, 7.8 | Disabled by default [130] |
Enabled by default | Yes | No [citation needed] |
No [citation needed] |
No | No [citation needed] |
Yes | Yes[147] | Unknown | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | |
| 10 | Windows Phone 8 | Disabled by default | Enabled by default | Yes | Disabled by default [149] |
Disabled by default [149] |
No | No [citation needed] |
Yes | Yes[150] | Mitigated | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | ||
| 11 | Windows Phone 8.1 | Disabled by default | Enabled by default | Yes | Yes[151] | Yes[151] | No | No [citation needed] |
Yes | Yes | Mitigated | Not affected | Vulnerable | Only as fallback [n 15][152][153] |
Vulnerable | Vulnerable | Only with 3rd party tools[n 26] | ||
| Microsoft Edge (13–15) (EdgeHTML-based) [n 27] |
13 | Windows 10 Mobile 1511 |
Disabled by default | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 14, 15 | Windows 10 Mobile 1607–1709 |
No[145] | Disabled by default | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Apple Safari [n 28] |
1 | Mac OS X 10.2, 10.3 | No[158] | Yes | Yes | No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |
| 2–5 | Mac OS X 10.4, 10.5, Win XP | No | Yes | Yes | No | No | No | since v3.2 | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 3–5 | Vista, Win 7 | No | Yes | Yes | No | No | No | since v3.2 | No | Yes[147] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 4–6 | Mac OS X 10.6, 10.7 | No | Yes | Yes | No | No | No | Yes | Yes[75] | Yes[76] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 6 | OS X 10.8 | No | Yes | Yes | No | No | No | Yes | Yes | Yes[76] | Mitigated [n 29] |
Not affected | Mitigated [n 30] |
Vulnerable [n 30] |
Mitigated [164] |
Vulnerable | No | ||
| 7, 9 | OS X 10.9 | No | Yes | Yes | Yes[165] | Yes[165] | No | Yes | Yes | Yes | Mitigated [160] |
Not affected | Mitigated [n 30] |
Vulnerable [n 30] |
Mitigated [164] |
Vulnerable | No | ||
| 8–10 | OS X 10.10 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 30] |
Lowest priority [166][n 30] |
Mitigated [164] |
Mitigated [167] |
No | ||
| 9–11 | OS X 10.11 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Lowest priority | Mitigated | Mitigated | No | ||
| 10–13 | macOS 10.12, 10.13 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 12–14 | macOS 10.14 | No | No | Yes | Yes | Yes | Yes (since macOS 10.14.4)[168] | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 13, 14 | 15 | macOS 10.15 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 14 | 15 | macOS 11 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | |
| 15 | macOS 12 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Apple Safari (mobile) [n 31] |
3 | iPhone OS 1, 2 | No[172] | Yes | Yes | No | No | No | No | No | No | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |
| 4, 5 | iPhone OS 3, iOS 4 | No | Yes | Yes | No | No | No | Yes[173] | Yes | since iOS 4[147] | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 5, 6 | iOS 5, 6 | No | Yes | Yes | Yes[169] | Yes[169] | No | Yes | Yes | Yes | Vulnerable | Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 7 | iOS 7 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes[174] | Mitigated [175] |
Not affected | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| 8 | iOS 8 | No | Yes | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Mitigated [n 30] |
Lowest priority [176][n 30] |
Mitigated [177] |
Mitigated [178] |
No | ||
| 9 | iOS 9 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Lowest priority | Mitigated | Mitigated | No | ||
| 10, 11 | iOS 10, 11 | No | No | Yes | Yes | Yes | No | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 12 | iOS 12 | No | No | Yes | Yes | Yes | Yes (since iOS 12.2)[168] | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| 13, 14 | iOS 13, 14 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| iPadOS 13, 14 | |||||||||||||||||||
| 15 | iOS 15 | No | No | Yes | Yes | Yes | Yes | Yes | Yes | Yes | Mitigated | Not affected | Not affected | Disabled by default[n 16] | Mitigated | Mitigated | No | ||
| iPadOS 15 | |||||||||||||||||||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV [n 3] |
SHA-2 | ECDSA | BEAST[n 4] | CRIME[n 5] | POODLE (SSLv3)[n 6] | RC4[n 7] | FREAK[77][78] | Logjam | Protocol selection by user | |
| Google Android OS [179] |
Android 1.0–4.0.4 | No | Enabled by default | Yes | No | No | No | Unknown | Yes[75] | since 3.0[147][76] | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | ||
| Android 4.1–4.4.4 | No | Enabled by default | Yes | Disabled by default[180] | Disabled by default[180] | No | Unknown | Yes | Yes | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |||
| Android 5.0–5.0.2 | No | Enabled by default | Yes | Yes[180][181] | Yes[180][181] | No | Unknown | Yes | Yes | Unknown | Unknown | Vulnerable | Vulnerable | Vulnerable | Vulnerable | No | |||
| Android 5.1–5.1.1 | No | Disabled by default [citation needed] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Only as fallback [n 15] |
Mitigated | Mitigated | No | |||
| Android 6.0–7.1.2 | No | Disabled by default [citation needed] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 8.0–8.1 | No | No [182] |
Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 9 | No | No | Yes | Yes | Yes | No | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 10 | No | No | Yes | Yes | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 11 | No | No | Yes | Yes | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 12 / 12L | No | No | Unknown | Unknown | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Android 13 | No | No | Unknown | Unknown | Yes | Yes | Unknown | Yes | Yes | Unknown | Unknown | Not affected | Disabled by default | Mitigated | Mitigated | No | |||
| Browser | Version | Platforms | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 (deprecated) | TLS 1.1 (deprecated) | TLS 1.2 | TLS 1.3 | EV certificate | SHA-2 certificate | ECDSA certificate | BEAST | CRIME | POODLE (SSLv3) | RC4 | FREAK | Logjam | Protocol selection by user | |
| Color or Note | Significance | ||||||||||||||||||
| Browser version | Platform | ||||||||||||||||||
| Browser version | Operating system | Future release; under development | |||||||||||||||||
| Browser version | Operating system | Current latest release | |||||||||||||||||
| Browser version | Operating system | Former release; still supported | |||||||||||||||||
| Browser version | Operating system | Former release; long-term support still active, but will end in less than 12 months | |||||||||||||||||
| Browser version | Operating system | Former release; no longer supported | |||||||||||||||||
| n/a | Operating system | Mixed / Unspecified | |||||||||||||||||
| Operating system (Version+) | Minimum required operating system version (for supported versions of the browser) | ||||||||||||||||||
| Operating system | No longer supported for this operating system |
Notes
- ^ Does the browser have mitigations or is not vulnerable for the known attacks. Note actual security depends on other factors such as negotiated cipher, encryption strength, etc. (see § Cipher table).
- ^ Whether a user or administrator can choose the protocols to be used or not. If yes, several attacks such as BEAST (vulnerable in SSL 3.0 and TLS 1.0) or POODLE (vulnerable in SSL 3.0) can be avoided.
- ^ a b Whether EV SSL and DV SSL (normal SSL) can be distinguished by indicators (green lock icon, green address bar, etc.) or not.
- ^ a b e.g. 1/n-1 record splitting.
- ^ a b e.g. Disabling header compression in HTTPS/SPDY.
- ^ a b
- Complete mitigations; disabling SSL 3.0 itself, “anti-POODLE record splitting”. “Anti-POODLE record splitting” is effective only with client-side implementation and valid according to the SSL 3.0 specification, however, it may also cause compatibility issues due to problems in server-side implementations.
- Partial mitigations; disabling fallback to SSL 3.0, TLS_FALLBACK_SCSV, disabling cipher suites with CBC mode of operation. If the server also supports TLS_FALLBACK_SCSV, the POODLE attack will fail against this combination of server and browser, but connections where the server does not support TLS_FALLBACK_SCSV and does support SSL 3.0 will still be vulnerable. If disabling cipher suites with CBC mode of operation in SSL 3.0, only cipher suites with RC4 are available, RC4 attacks become easier.
- When disabling SSL 3.0 manually, POODLE attack will fail.
- ^ a b
- Complete mitigation; disabling cipher suites with RC4.
- Partial mitigations to keeping compatibility with old systems; setting the priority of RC4 to lower.
- ^ Google Chrome (and Chromium) supports TLS 1.0, and TLS 1.1 from version 22 (it was added, then dropped from version 21). TLS 1.2 support has been added, then dropped from Chrome 29.[79][80][81]
- ^ Uses the TLS implementation provided by BoringSSL for Android, OS X, and Windows[82] or by NSS for Linux. Google is switching the TLS library used in Chrome to BoringSSL from NSS completely.
- ^ a b c d e f g h i j k l m n o p q r s t u v w x y z aa ab ac ad ae af ag ah ai configure enabling/disabling of each protocols via setting/option (menu name is dependent on browsers)
- ^ a b c d e f g h i j k l configure the maximum and the minimum version of enabling protocols with command-line option
- ^ TLS_FALLBACK_SCSV is implemented.[90] Fallback to SSL 3.0 is disabled since version 39.[91]
- ^ In addition to TLS_FALLBACK_SCSV and disabling a fallback to SSL 3.0, SSL 3.0 itself is disabled by default.[91]
- ^ a b c configure the minimum version of enabling protocols via chrome://flags[95] (the maximum version can be configured with command-line option)
- ^ a b c d e f g Only when no cipher suites with other than RC4 is available, cipher suites with RC4 will be used as a fallback.
- ^ a b c d e f g h i j k l m n o p q r s t u v w x y z aa ab ac ad ae af ag ah ai aj All RC4 cipher suites are disabled by default.
- ^ Uses the TLS implementation provided by NSS. As of Firefox 22, Firefox supports only TLS 1.0 despite the bundled NSS supporting TLS 1.1. Since Firefox 23, TLS 1.1 can be enabled, but was not enabled by default due to issues. Firefox 24 has TLS 1.2 support disabled by default. TLS 1.1 and TLS 1.2 have been enabled by default in Firefox 27 release.
- ^ a b c d e f g h i j k l m n configure the maximum and the minimum version of enabling protocols via about:config
- ^ SSL 3.0 itself is disabled by default.[113] In addition, fallback to SSL 3.0 is disabled since version 34,[115] and TLS_FALLBACK_SCSV is implemented since 35.0 and ESR 31.3.[113][116]
- ^ a b c d e f IE uses the TLS implementation of the Microsoft Windows operating system provided by the SChannel security support provider. TLS 1.1 and 1.2 are disabled by default until IE11.[126][127]
- ^ a b Windows NT 3.1 supports IE 1–2, Windows NT 3.5 supports IE 1–3, Windows NT 3.51 and Windows NT 4.0 supports IE 1–6
- ^ a b c d Windows XP as well as Server 2003 and older support only weak ciphers like 3DES and RC4 out of the box.[131] The weak ciphers of these SChannel version are not only used for IE, but also for other Microsoft products running on this OS, like Office or Windows Update. Only Windows Server 2003 can get a manual update to support AES ciphers by KB948963[132]
- ^ a b c d MS13-095 or MS14-049 for Windows Server 2003, Windows XP x64 and Windows XP SP3 (32-bit)
- ^ RC4 can be disabled except as a fallback (Only when no cipher suites with other than RC4 is available, cipher suites with RC4 will be used as a fallback.)[138]
- ^ a b c d Fallback to SSL 3.0 is sites blocked by default in Internet Explorer 11 for Protected Mode.[140][141] SSL 3.0 is disabled by default in Internet Explorer 11 since April 2015.[142]
- ^ a b c Could be disabled via registry editing but need 3rd Party tools to do this.[148]
- ^ Edge (formerly known as Project Spartan) is based on a fork of the Internet Explorer 11 rendering engine.
- ^ Safari uses the operating system implementation on Mac OS X, Windows (XP, Vista, 7)[154] with unknown version,[155] Safari 5 is the last version available for Windows. OS X 10.8 on have SecureTransport support for TLS 1.1 and 1.2[156] Qualys SSL report simulates Safari 5.1.9 connecting with TLS 1.0 not 1.1 or 1.2[157]
- ^ In September 2013, Apple implemented BEAST mitigation in OS X 10.8 (Mountain Lion), but it was not turned on by default, resulting in Safari still being theoretically vulnerable to the BEAST attack on that platform.[159][160] BEAST mitigation has been enabled by default from OS X 10.8.5 updated in February 2014.[161]
- ^ a b c d e f g h Because Apple removed support for all CBC protocols in SSL 3.0 to mitigate POODLE,[162][163] this leaves only RC4, which is also completely broken by the RC4 attacks in SSL 3.0.
- ^ Mobile Safari and third-party software utilizing the system UIWebView library use the iOS operating system implementation, which supports TLS 1.2 as of iOS 5.0.[169][170][171]
Libraries
Most SSL and TLS programming libraries are free and open source software.
- BoringSSL, a fork of OpenSSL for Chrome/Chromium and Android as well as other Google applications.
- Botan, a BSD-licensed cryptographic library written in C++.
- BSAFE Micro Edition Suite: a multi-platform implementation of TLS written in C using a FIPS-validated cryptographic module
- BSAFE SSL-J: a TLS library providing both a proprietary API and JSSE API, using FIPS-validated cryptographic module
- cryptlib: a portable open source cryptography library (includes TLS/SSL implementation)
- Delphi programmers may use a library called Indy which utilizes OpenSSL or alternatively ICS which supports TLS 1.3 now.
- GnuTLS: a free implementation (LGPL licensed)
- Java Secure Socket Extension (JSSE): the Java API and provider implementation (named SunJSSE)[183]
- LibreSSL: a fork of OpenSSL by OpenBSD project.
- MatrixSSL: a dual licensed implementation
- mbed TLS (previously PolarSSL): A tiny SSL library implementation for embedded devices that is designed for ease of use
- Network Security Services: FIPS 140 validated open source library
- OpenSSL: a free implementation (BSD license with some extensions)
- SChannel: an implementation of SSL and TLS Microsoft Windows as part of its package.
- Secure Transport: an implementation of SSL and TLS used in OS X and iOS as part of their packages.
- wolfSSL (previously CyaSSL): Embedded SSL/TLS Library with a strong focus on speed and size.
| Implementation | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 |
|---|---|---|---|---|---|---|
| Botan | No | No[184] | Yes | Yes | Yes | |
| BSAFE Micro Edition Suite | No | Disabled by default | Yes | Yes | Yes | In development |
| BSAFE SSL-J | No | Disabled by default | Yes | Yes | Yes | Yes |
| cryptlib | No | Disabled by default at compile time | Yes | Yes | Yes | |
| GnuTLS | No[a] | Disabled by default[185] | Yes | Yes | Yes | Yes[186] |
| JSSE | No[a] | Disabled by default[187] | Disabled by default[188] | Disabled by default[188] | Yes | Yes |
| LibreSSL | No[189] | No[190] | Yes | Yes | Yes | As of version 3.2.2 [191][192] |
| MatrixSSL | No | Disabled by default at compile time[193] | Yes | Yes | Yes | yes (draft version) |
| mbed TLS (previously PolarSSL) | No | Disabled by default[194] | Yes | Yes | Yes | |
| Network Security Services | No[b] | Disabled by default[195] | Yes | Yes[196] | Yes[197] | Yes[198] |
| OpenSSL | No[199] | Enabled by default | Yes | Yes[200] | Yes[200] | Yes[201] |
| SChannel XP / 2003[202] | Disabled by default by MSIE 7 | Enabled by default | Enabled by default by MSIE 7 | No | No | No |
| SChannel Vista[203] | Disabled by default | Enabled by default | Yes | No | No | No |
| SChannel 2008[203] | Disabled by default | Enabled by default | Yes | Disabled by default (KB4019276)[135] | Disabled by default (KB4019276)[135] | No |
| SChannel 7 / 2008 R2[204] | Disabled by default | Disabled by default in MSIE 11 | Yes | Enabled by default by MSIE 11 | Enabled by default by MSIE 11 | No |
| SChannel 8 / 2012[204] | Disabled by default | Enabled by default | Yes | Disabled by default | Disabled by default | No |
| SChannel 8.1 / 2012 R2, 10 v1507 & v1511[204] | Disabled by default | Disabled by default in MSIE 11 | Yes | Yes | Yes | No |
| SChannel 10 v1607 / 2016[145] | No | Disabled by default | Yes | Yes | Yes | No |
| SChannel 10 v1903[205] | No | Disabled by default | Yes | Yes | Yes | No |
| SChannel 10 v21H1[206] | No | Disabled by default | Yes | Yes | Yes | No |
| SChannel 11 / 2022[207] | No | Disabled by default | Yes | Yes | Yes | Yes |
| Secure Transport OS X 10.2–10.8 / iOS 1–4 | Yes | Yes | Yes | No | No | |
| Secure Transport OS X 10.9–10.10 / iOS 5–8 | No[c] | Yes | Yes | Yes[c] | Yes[c] | |
| Secure Transport OS X 10.11 / iOS 9 | No | No[c] | Yes | Yes | Yes | |
| Seed7 TLS/SSL Library | No | Yes | Yes | Yes | Yes | |
| wolfSSL (previously CyaSSL) | No | Disabled by default[208] | Yes | Yes | Yes | Yes[209] |
| Implementation | SSL 2.0 (insecure) | SSL 3.0 (insecure) | TLS 1.0 | TLS 1.1 | TLS 1.2 | TLS 1.3 |
- ^ SSL 2.0 client hello is supported for backward compatibility reasons even though SSL 2.0 is not supported.
- ^ Server-side implementation of the SSL/TLS protocol still supports processing of received v2-compatible client hello messages. [210]
- ^ Secure Transport: SSL 2.0 was discontinued in OS X 10.8. SSL 3.0 was discontinued in OS X 10.11 and iOS 9. TLS 1.1 and 1.2 are available on iOS 5.0 and later, and OS X 10.9 and later. [211]
[212]
A paper presented at the 2012 ACM conference on computer and communications security[213] showed that few applications used some of these SSL libraries correctly, leading to vulnerabilities. According to the authors
“the root cause of most of these vulnerabilities is the terrible design of the APIs to the underlying SSL libraries. Instead of expressing high-level security properties of network tunnels such as confidentiality and authentication, these APIs expose low-level details of the SSL protocol to application developers. As a consequence, developers often use SSL APIs incorrectly, misinterpreting and misunderstanding their manifold parameters, options, side effects, and return values.”
Other uses
The Simple Mail Transfer Protocol (SMTP) can also be protected by TLS. These applications use public key certificates to verify the identity of endpoints.
TLS can also be used for tunnelling an entire network stack to create a VPN, which is the case with OpenVPN and OpenConnect. Many vendors have by now married TLS’s encryption and authentication capabilities with authorization. There has also been substantial development since the late 1990s in creating client technology outside of Web-browsers, in order to enable support for client/server applications. Compared to traditional IPsec VPN technologies, TLS has some inherent advantages in firewall and NAT traversal that make it easier to administer for large remote-access populations.
TLS is also a standard method for protecting Session Initiation Protocol (SIP) application signaling. TLS can be used for providing authentication and encryption of the SIP signalling associated with VoIP and other SIP-based applications.[214]
Security
Attacks against TLS/SSL
Significant attacks against TLS/SSL are listed below.
In February 2015, IETF issued an informational RFC[215] summarizing the various known attacks against TLS/SSL.
Renegotiation attack
A vulnerability of the renegotiation procedure was discovered in August 2009 that can lead to plaintext injection attacks against SSL 3.0 and all current versions of TLS.[216] For example, it allows an attacker who can hijack an https connection to splice their own requests into the beginning of the conversation the client has with the web server. The attacker can’t actually decrypt the client–server communication, so it is different from a typical man-in-the-middle attack. A short-term fix is for web servers to stop allowing renegotiation, which typically will not require other changes unless client certificate authentication is used. To fix the vulnerability, a renegotiation indication extension was proposed for TLS. It will require the client and server to include and verify information about previous handshakes in any renegotiation handshakes.[217] This extension has become a proposed standard and has been assigned the number RFC 5746. The RFC has been implemented by several libraries.[218][219][220]
Downgrade attacks: FREAK attack and Logjam attack
A protocol downgrade attack (also called a version rollback attack) tricks a web server into negotiating connections with previous versions of TLS (such as SSLv2) that have long since been abandoned as insecure.
Previous modifications to the original protocols, like False Start[221] (adopted and enabled by Google Chrome[222]) or Snap Start, reportedly introduced limited TLS protocol downgrade attacks[223] or allowed modifications to the cipher suite list sent by the client to the server. In doing so, an attacker might succeed in influencing the cipher suite selection in an attempt to downgrade the cipher suite negotiated to use either a weaker symmetric encryption algorithm or a weaker key exchange.[224] A paper presented at an ACM conference on computer and communications security in 2012 demonstrated that the False Start extension was at risk: in certain circumstances it could allow an attacker to recover the encryption keys offline and to access the encrypted data.[225]
Encryption downgrade attacks can force servers and clients to negotiate a connection using cryptographically weak keys. In 2014, a man-in-the-middle attack called FREAK was discovered affecting the OpenSSL stack, the default Android web browser, and some Safari browsers.[226] The attack involved tricking servers into negotiating a TLS connection using cryptographically weak 512 bit encryption keys.
Logjam is a security exploit discovered in May 2015 that exploits the option of using legacy “export-grade” 512-bit Diffie–Hellman groups dating back to the 1990s.[227] It forces susceptible servers to downgrade to cryptographically weak 512-bit Diffie–Hellman groups. An attacker can then deduce the keys the client and server determine using the Diffie–Hellman key exchange.
Cross-protocol attacks: DROWN
The DROWN attack is an exploit that attacks servers supporting contemporary SSL/TLS protocol suites by exploiting their support for the obsolete, insecure, SSLv2 protocol to leverage an attack on connections using up-to-date protocols that would otherwise be secure.[228][229] DROWN exploits a vulnerability in the protocols used and the configuration of the server, rather than any specific implementation error. Full details of DROWN were announced in March 2016, together with a patch for the exploit. At that time, more than 81,000 of the top 1 million most popular websites were among the TLS protected websites that were vulnerable to the DROWN attack.[229]
BEAST attack
On September 23, 2011 researchers Thai Duong and Juliano Rizzo demonstrated a proof of concept called BEAST (Browser Exploit Against SSL/TLS)[230] using a Java applet to violate same origin policy constraints, for a long-known cipher block chaining (CBC) vulnerability in TLS 1.0:[231][232] an attacker observing 2 consecutive ciphertext blocks C0, C1 can test if the plaintext block P1 is equal to x by choosing the next plaintext block P2 = x ⊕ {displaystyle oplus } 
C0 ⊕ {displaystyle oplus }

C1; as per CBC operation, C2 = E(C1 ⊕ {displaystyle oplus }

P2) = E(C1 ⊕ {displaystyle oplus }

x ⊕ {displaystyle oplus }

C0 ⊕ {displaystyle oplus }

C1) = E(C0 ⊕ {displaystyle oplus }

x), which will be equal to C1 if x = P1. Practical exploits had not been previously demonstrated for this vulnerability, which was originally discovered by Phillip Rogaway[233] in 2002. The vulnerability of the attack had been fixed with TLS 1.1 in 2006, but TLS 1.1 had not seen wide adoption prior to this attack demonstration.
RC4 as a stream cipher is immune to BEAST attack. Therefore, RC4 was widely used as a way to mitigate BEAST attack on the server side. However, in 2013, researchers found more weaknesses in RC4. Thereafter enabling RC4 on server side was no longer recommended.[234]
Chrome and Firefox themselves are not vulnerable to BEAST attack,[83][104] however, Mozilla updated their NSS libraries to mitigate BEAST-like attacks. NSS is used by Mozilla Firefox and Google Chrome to implement SSL. Some web servers that have a broken implementation of the SSL specification may stop working as a result.[235]
Microsoft released Security Bulletin MS12-006 on January 10, 2012, which fixed the BEAST vulnerability by changing the way that the Windows Secure Channel (SChannel) component transmits encrypted network packets from the server end.[236] Users of Internet Explorer (prior to version 11) that run on older versions of Windows (Windows 7, Windows 8 and Windows Server 2008 R2) can restrict use of TLS to 1.1 or higher.
Apple fixed BEAST vulnerability by implementing 1/n-1 split and turning it on by default in OS X Mavericks, released on October 22, 2013.[237]
CRIME and BREACH attacks
The authors of the BEAST attack are also the creators of the later CRIME attack, which can allow an attacker to recover the content of web cookies when data compression is used along with TLS.[238][239] When used to recover the content of secret authentication cookies, it allows an attacker to perform session hijacking on an authenticated web session.
While the CRIME attack was presented as a general attack that could work effectively against a large number of protocols, including but not limited to TLS, and application-layer protocols such as SPDY or HTTP, only exploits against TLS and SPDY were demonstrated and largely mitigated in browsers and servers. The CRIME exploit against HTTP compression has not been mitigated at all, even though the authors of CRIME have warned that this vulnerability might be even more widespread than SPDY and TLS compression combined. In 2013 a new instance of the CRIME attack against HTTP compression, dubbed BREACH, was announced. Based on the CRIME attack a BREACH attack can extract login tokens, email addresses or other sensitive information from TLS encrypted web traffic in as little as 30 seconds (depending on the number of bytes to be extracted), provided the attacker tricks the victim into visiting a malicious web link or is able to inject content into valid pages the user is visiting (ex: a wireless network under the control of the attacker).[240] All versions of TLS and SSL are at risk from BREACH regardless of the encryption algorithm or cipher used.[241] Unlike previous instances of CRIME, which can be successfully defended against by turning off TLS compression or SPDY header compression, BREACH exploits HTTP compression which cannot realistically be turned off, as virtually all web servers rely upon it to improve data transmission speeds for users.[240] This is a known limitation of TLS as it is susceptible to chosen-plaintext attack against the application-layer data it was meant to protect.
Timing attacks on padding
Earlier TLS versions were vulnerable against the padding oracle attack discovered in 2002. A novel variant, called the Lucky Thirteen attack, was published in 2013.
Some experts[66] also recommended avoiding Triple-DES CBC. Since the last supported ciphers developed to support any program using Windows XP’s SSL/TLS library like Internet Explorer on Windows XP are RC4 and Triple-DES, and since RC4 is now deprecated (see discussion of RC4 attacks), this makes it difficult to support any version of SSL for any program using this library on XP.
A fix was released as the Encrypt-then-MAC extension to the TLS specification, released as RFC 7366.[242] The Lucky Thirteen attack can be mitigated in TLS 1.2 by using only AES_GCM ciphers; AES_CBC remains vulnerable.[citation needed]
POODLE attack
On October 14, 2014, Google researchers published a vulnerability in the design of SSL 3.0, which makes CBC mode of operation with SSL 3.0 vulnerable to a padding attack (CVE- 2014-3566). They named this attack POODLE (Padding Oracle On Downgraded Legacy Encryption). On average, attackers only need to make 256 SSL 3.0 requests to reveal one byte of encrypted messages.[73]
Although this vulnerability only exists in SSL 3.0 and most clients and servers support TLS 1.0 and above, all major browsers voluntarily downgrade to SSL 3.0 if the handshakes with newer versions of TLS fail unless they provide the option for a user or administrator to disable SSL 3.0 and the user or administrator does so[citation needed]. Therefore, the man-in-the-middle can first conduct a version rollback attack and then exploit this vulnerability.[73]
On December 8, 2014, a variant of POODLE was announced that impacts TLS implementations that do not properly enforce padding byte requirements.[243]
RC4 attacks
Despite the existence of attacks on RC4 that broke its security, cipher suites in SSL and TLS that were based on RC4 were still considered secure prior to 2013 based on the way in which they were used in SSL and TLS. In 2011, the RC4 suite was actually recommended as a work around for the BEAST attack.[244] New forms of attack disclosed in March 2013 conclusively demonstrated the feasibility of breaking RC4 in TLS, suggesting it was not a good workaround for BEAST.[72] An attack scenario was proposed by AlFardan, Bernstein, Paterson, Poettering and Schuldt that used newly discovered statistical biases in the RC4 key table[245] to recover parts of the plaintext with a large number of TLS encryptions.[246][247] An attack on RC4 in TLS and SSL that requires 13 × 220 encryptions to break RC4 was unveiled on 8 July 2013 and later described as “feasible” in the accompanying presentation at a USENIX Security Symposium in August 2013.[248][249] In July 2015, subsequent improvements in the attack make it increasingly practical to defeat the security of RC4-encrypted TLS.[250]
As many modern browsers have been designed to defeat BEAST attacks (except Safari for Mac OS X 10.7 or earlier, for iOS 6 or earlier, and for Windows; see § Web browsers), RC4 is no longer a good choice for TLS 1.0. The CBC ciphers which were affected by the BEAST attack in the past have become a more popular choice for protection.[66] Mozilla and Microsoft recommend disabling RC4 where possible.[251][252] RFC 7465 prohibits the use of RC4 cipher suites in all versions of TLS.
On September 1, 2015, Microsoft, Google and Mozilla announced that RC4 cipher suites would be disabled by default in their browsers (Microsoft Edge, Internet Explorer 11 on Windows 7/8.1/10, Firefox, and Chrome) in early 2016.[253][254][255]
Truncation attack
A TLS (logout) truncation attack blocks a victim’s account logout requests so that the user unknowingly remains logged into a web service. When the request to sign out is sent, the attacker injects an unencrypted TCP FIN message (no more data from sender) to close the connection. The server therefore doesn’t receive the logout request and is unaware of the abnormal termination.[256]
Published in July 2013,[257][258] the attack causes web services such as Gmail and Hotmail to display a page that informs the user that they have successfully signed-out, while ensuring that the user’s browser maintains authorization with the service, allowing an attacker with subsequent access to the browser to access and take over control of the user’s logged-in account. The attack does not rely on installing malware on the victim’s computer; attackers need only place themselves between the victim and the web server (e.g., by setting up a rogue wireless hotspot).[256] This vulnerability also requires access to the victim’s computer. Another possibility is when using FTP the data connection can have a false FIN in the data stream, and if the protocol rules for exchanging close_notify alerts is not adhered to a file can be truncated.
Unholy PAC attack
This attack, discovered in mid-2016, exploits weaknesses in the Web Proxy Autodiscovery Protocol (WPAD) to expose the URL that a web user is attempting to reach via a TLS-enabled web link.[259] Disclosure of a URL can violate a user’s privacy, not only because of the website accessed, but also because URLs are sometimes used to authenticate users. Document sharing services, such as those offered by Google and Dropbox, also work by sending a user a security token that’s included in the URL. An attacker who obtains such URLs may be able to gain full access to a victim’s account or data.
The exploit works against almost all browsers and operating systems.
Sweet32 attack
The Sweet32 attack breaks all 64-bit block ciphers used in CBC mode as used in TLS by exploiting a birthday attack and either a man-in-the-middle attack or injection of a malicious JavaScript into a web page. The purpose of the man-in-the-middle attack or the JavaScript injection is to allow the attacker to capture enough traffic to mount a birthday attack.[260]
Implementation errors: Heartbleed bug, BERserk attack, Cloudflare bug
The Heartbleed bug is a serious vulnerability specific to the implementation of SSL/TLS in the popular OpenSSL cryptographic software library, affecting versions 1.0.1 to 1.0.1f. This weakness, reported in April 2014, allows attackers to steal private keys from servers that should normally be protected.[261] The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret private keys associated with the public certificates used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data directly from the services and users and to impersonate services and users.[262] The vulnerability is caused by a buffer over-read bug in the OpenSSL software, rather than a defect in the SSL or TLS protocol specification.
In September 2014, a variant of Daniel Bleichenbacher’s PKCS#1 v1.5 RSA Signature Forgery vulnerability[263] was announced by Intel Security Advanced Threat Research. This attack, dubbed BERserk, is a result of incomplete ASN.1 length decoding of public key signatures in some SSL implementations, and allows a man-in-the-middle attack by forging a public key signature.[264]
In February 2015, after media reported the hidden pre-installation of Superfish adware on some Lenovo notebooks,[265] a researcher found a trusted root certificate on affected Lenovo machines to be insecure, as the keys could easily be accessed using the company name, Komodia, as a passphrase.[266] The Komodia library was designed to intercept client-side TLS/SSL traffic for parental control and surveillance, but it was also used in numerous adware programs, including Superfish, that were often surreptitiously installed unbeknownst to the computer user. In turn, these potentially unwanted programs installed the corrupt root certificate, allowing attackers to completely control web traffic and confirm false websites as authentic.
In May 2016, it was reported that dozens of Danish HTTPS-protected websites belonging to Visa Inc. were vulnerable to attacks allowing hackers to inject malicious code and forged content into the browsers of visitors.[267] The attacks worked because the TLS implementation used on the affected servers incorrectly reused random numbers (nonces) that are intended to be used only once, ensuring that each TLS handshake is unique.[267]
In February 2017, an implementation error caused by a single mistyped character in code used to parse HTML created a buffer overflow error on Cloudflare servers. Similar in its effects to the Heartbleed bug discovered in 2014, this overflow error, widely known as Cloudbleed, allowed unauthorized third parties to read data in the memory of programs running on the servers—data that should otherwise have been protected by TLS.[268]
Survey of websites vulnerable to attacks
As of July 2021[update], the Trustworthy Internet Movement estimated the ratio of websites that are vulnerable to TLS attacks.[71]
| Attacks | Security | |||
|---|---|---|---|---|
| Insecure | Depends | Secure | Other | |
| Renegotiation attack | 0.1% support insecure renegotiation |
<0.1% support both |
99.2% support secure renegotiation |
0.7% no support |
| RC4 attacks | 0.4% support RC4 suites used with modern browsers |
6.5% support some RC4 suites |
93.1% no support |
N/A |
| TLS Compression (CRIME attack) | >0.0% vulnerable |
N/A | N/A | N/A |
| Heartbleed | >0.0% vulnerable |
N/A | N/A | N/A |
| ChangeCipherSpec injection attack | 0.1% vulnerable and exploitable |
0.2% vulnerable, not exploitable |
98.5% not vulnerable |
1.2% unknown |
| POODLE attack against TLS (Original POODLE against SSL 3.0 is not included) |
0.1% vulnerable and exploitable |
0.1% vulnerable, not exploitable |
99.8% not vulnerable |
0.2% unknown |
| Protocol downgrade | 6.6% Downgrade defence not supported |
N/A | 72.3% Downgrade defence supported |
21.0% unknown |
Forward secrecy
Forward secrecy is a property of cryptographic systems which ensures that a session key derived from a set of public and private keys will not be compromised if one of the private keys is compromised in the future.[269] Without forward secrecy, if the server’s private key is compromised, not only will all future TLS-encrypted sessions using that server certificate be compromised, but also any past sessions that used it as well (provided of course that these past sessions were intercepted and stored at the time of transmission).[270] An implementation of TLS can provide forward secrecy by requiring the use of ephemeral Diffie–Hellman key exchange to establish session keys, and some notable TLS implementations do so exclusively: e.g., Gmail and other Google HTTPS services that use OpenSSL.[271] However, many clients and servers supporting TLS (including browsers and web servers) are not configured to implement such restrictions.[272][273] In practice, unless a web service uses Diffie–Hellman key exchange to implement forward secrecy, all of the encrypted web traffic to and from that service can be decrypted by a third party if it obtains the server’s master (private) key; e.g., by means of a court order.[274]
Even where Diffie–Hellman key exchange is implemented, server-side session management mechanisms can impact forward secrecy. The use of TLS session tickets (a TLS extension) causes the session to be protected by AES128-CBC-SHA256 regardless of any other negotiated TLS parameters, including forward secrecy ciphersuites, and the long-lived TLS session ticket keys defeat the attempt to implement forward secrecy.[275][276][277] Stanford University research in 2014 also found that of 473,802 TLS servers surveyed, 82.9% of the servers deploying ephemeral Diffie–Hellman (DHE) key exchange to support forward secrecy were using weak Diffie–Hellman parameters. These weak parameter choices could potentially compromise the effectiveness of the forward secrecy that the servers sought to provide.[278]
Since late 2011, Google has provided forward secrecy with TLS by default to users of its Gmail service, along with Google Docs and encrypted search, among other services.[279] Since November 2013, Twitter has provided forward secrecy with TLS to users of its service.[280] As of August 2019[update], about 80% of TLS-enabled websites are configured to use cipher suites that provide forward secrecy to most web browsers.[71]
TLS interception
TLS interception (or HTTPS interception if applied particularly to that protocol) is the practice of intercepting an encrypted data stream in order to decrypt it, read and possibly manipulate it, and then re-encrypt it and send the data on its way again. This is done by way of a “transparent proxy”: the interception software terminates the incoming TLS connection, inspects the HTTP plaintext, and then creates a new TLS connection to the destination.[281]
TLS / HTTPS interception is used as an information security measure by network operators in order to be able to scan for and protect against the intrusion of malicious content into the network, such as computer viruses and other malware.[281] Such content could otherwise not be detected as long as it is protected by encryption, which is increasingly the case as a result of the routine use of HTTPS and other secure protocols.
A significant drawback of TLS / HTTPS interception is that it introduces new security risks of its own. One notable limitation is that it provides a point where network traffic is available unencrypted thus giving attackers an incentive to attack this point in particular in order to gain access to otherwise secure content. The interception also allows the network operator, or persons who gain access to its interception system, to perform man-in-the-middle attacks against network users. A 2017 study found that “HTTPS interception has become startlingly widespread, and that interception products as a class have a dramatically negative impact on connection security”.[281]
Protocol details
The TLS protocol exchanges records, which encapsulate the data to be exchanged in a specific format (see below). Each record can be compressed, padded, appended with a message authentication code (MAC), or encrypted, all depending on the state of the connection. Each record has a content type field that designates the type of data encapsulated, a length field and a TLS version field. The data encapsulated may be control or procedural messages of the TLS itself, or simply the application data needed to be transferred by TLS. The specifications (cipher suite, keys etc.) required to exchange application data by TLS, are agreed upon in the “TLS handshake” between the client requesting the data and the server responding to requests. The protocol therefore defines both the structure of payloads transferred in TLS and the procedure to establish and monitor the transfer.
TLS handshake

 Simplified illustration of the full TLS 1.2 handshake with timing information.
Simplified illustration of the full TLS 1.2 handshake with timing information.
When the connection starts, the record encapsulates a “control” protocol – the handshake messaging protocol (content type 22). This protocol is used to exchange all the information required by both sides for the exchange of the actual application data by TLS. It defines the format of messages and the order of their exchange. These may vary according to the demands of the client and server – i.e., there are several possible procedures to set up the connection. This initial exchange results in a successful TLS connection (both parties ready to transfer application data with TLS) or an alert message (as specified below).
Basic TLS handshake
A typical connection example follows, illustrating a handshake where the server (but not the client) is authenticated by its certificate:
- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and suggested compression methods. If the client is attempting to perform a resumed handshake, it may send a session ID. If the client can use Application-Layer Protocol Negotiation, it may include a list of supported application protocols, such as HTTP/2.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. To confirm or allow resumed handshakes the server may send a session ID. The chosen protocol version should be the highest that both the client and server support. For example, if the client supports TLS version 1.1 and the server supports version 1.2, version 1.1 should be selected; version 1.2 should not be selected.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).[282]
- The server sends its ServerKeyExchange message (depending on the selected cipher suite, this may be omitted by the server). This message is sent for all DHE, ECDHE and DH_anon cipher suites.[7]
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the “master secret”. All other key data (session keys such as IV, symmetric encryption key, MAC key[283]) for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandom function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, “Everything I tell you from now on will be authenticated (and encrypted if encryption parameters were present in the server certificate).” The ChangeCipherSpec is itself a record-level protocol with content type of 20.
- The client sends an authenticated and encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client’s Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, “Everything I tell you from now on will be authenticated (and encrypted, if encryption was negotiated).”
- The server sends its authenticated and encrypted Finished message.
- The client performs the same decryption and verification procedure as the server did in the previous step.
- Application phase: at this point, the “handshake” is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be authenticated and optionally encrypted exactly like in their Finished message. Otherwise, the content type will return 25 and the client will not authenticate.
Client-authenticated TLS handshake
The following full example shows a client being authenticated (in addition to the server as in the example above; see mutual authentication) via TLS using certificates exchanged between both peers.
- Negotiation Phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. The server may also send a session id as part of the message to perform a resumed handshake.
- The server sends its Certificate message (depending on the selected cipher suite, this may be omitted by the server).[282]
- The server sends its ServerKeyExchange message (depending on the selected cipher suite, this may be omitted by the server). This message is sent for all DHE, ECDHE and DH_anon ciphersuites.[7]
- The server sends a CertificateRequest message, to request a certificate from the client.
- The server sends a ServerHelloDone message, indicating it is done with handshake negotiation.
- The client responds with a Certificate message, which contains the client’s certificate, but not it’s private key.
- The client sends a ClientKeyExchange message, which may contain a PreMasterSecret, public key, or nothing. (Again, this depends on the selected cipher.) This PreMasterSecret is encrypted using the public key of the server certificate.
- The client sends a CertificateVerify message, which is a signature over the previous handshake messages using the client’s certificate’s private key. This signature can be verified by using the client’s certificate’s public key. This lets the server know that the client has access to the private key of the certificate and thus owns the certificate.
- The client and server then use the random numbers and PreMasterSecret to compute a common secret, called the “master secret”. All other key data (“session keys”) for this connection is derived from this master secret (and the client- and server-generated random values), which is passed through a carefully designed pseudorandom function.
- The client now sends a ChangeCipherSpec record, essentially telling the server, “Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated). ” The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the client sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The server will attempt to decrypt the client’s Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the server sends a ChangeCipherSpec, telling the client, “Everything I tell you from now on will be authenticated (and encrypted if encryption was negotiated). ”
- The server sends its own encrypted Finished message.
- The client performs the same decryption and verification procedure as the server did in the previous step.
- Application phase: at this point, the “handshake” is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message.
Resumed TLS handshake
Public key operations (e.g., RSA) are relatively expensive in terms of computational power. TLS provides a secure shortcut in the handshake mechanism to avoid these operations: resumed sessions. Resumed sessions are implemented using session IDs or session tickets.
Apart from the performance benefit, resumed sessions can also be used for single sign-on, as it guarantees that both the original session and any resumed session originate from the same client. This is of particular importance for the FTP over TLS/SSL protocol, which would otherwise suffer from a man-in-the-middle attack in which an attacker could intercept the contents of the secondary data connections.[284]
TLS 1.3 handshake
The TLS 1.3 handshake was condensed to only one round trip compared to the two round trips required in previous versions of TLS/SSL.
First the client sends a clientHello message to the server that contains a list of supported ciphers in order of the client’s preference and makes a guess on what key algorithm will be used so that it can send a secret key to share if needed. By making a guess at what key algorithm will be used, the server eliminates a round trip. After receiving the clientHello, the server sends a serverHello with its key, a certificate, the chosen cipher suite and the finished message.
After the client receives the server’s finished message, it now is coordinated with the server on which cipher suite to use.[285]
Session IDs
In an ordinary full handshake, the server sends a session id as part of the ServerHello message. The client associates this session id with the server’s IP address and TCP port, so that when the client connects again to that server, it can use the session id to shortcut the handshake. In the server, the session id maps to the cryptographic parameters previously negotiated, specifically the “master secret”. Both sides must have the same “master secret” or the resumed handshake will fail (this prevents an eavesdropper from using a session id). The random data in the ClientHello and ServerHello messages virtually guarantee that the generated connection keys will be different from in the previous connection. In the RFCs, this type of handshake is called an abbreviated handshake. It is also described in the literature as a restart handshake.
- Negotiation phase:
- A client sends a ClientHello message specifying the highest TLS protocol version it supports, a random number, a list of suggested cipher suites and compression methods. Included in the message is the session id from the previous TLS connection.
- The server responds with a ServerHello message, containing the chosen protocol version, a random number, cipher suite and compression method from the choices offered by the client. If the server recognizes the session id sent by the client, it responds with the same session id. The client uses this to recognize that a resumed handshake is being performed. If the server does not recognize the session id sent by the client, it sends a different value for its session id. This tells the client that a resumed handshake will not be performed. At this point, both the client and server have the “master secret” and random data to generate the key data to be used for this connection.
- The server now sends a ChangeCipherSpec record, essentially telling the client, “Everything I tell you from now on will be encrypted.” The ChangeCipherSpec is itself a record-level protocol and has type 20 and not 22.
- Finally, the server sends an encrypted Finished message, containing a hash and MAC over the previous handshake messages.
- The client will attempt to decrypt the server’s Finished message and verify the hash and MAC. If the decryption or verification fails, the handshake is considered to have failed and the connection should be torn down.
- Finally, the client sends a ChangeCipherSpec, telling the server, “Everything I tell you from now on will be encrypted. ”
- The client sends its own encrypted Finished message.
- The server performs the same decryption and verification procedure as the client did in the previous step.
- Application phase: at this point, the “handshake” is complete and the application protocol is enabled, with content type of 23. Application messages exchanged between client and server will also be encrypted exactly like in their Finished message.
Session tickets
RFC 5077 extends TLS via use of session tickets, instead of session IDs. It defines a way to resume a TLS session without requiring that session-specific state is stored at the TLS server.
When using session tickets, the TLS server stores its session-specific state in a session ticket and sends the session ticket to the TLS client for storing. The client resumes a TLS session by sending the session ticket to the server, and the server resumes the TLS session according to the session-specific state in the ticket. The session ticket is encrypted and authenticated by the server, and the server verifies its validity before using its contents.
One particular weakness of this method with OpenSSL is that it always limits encryption and authentication security of the transmitted TLS session ticket to AES128-CBC-SHA256, no matter what other TLS parameters were negotiated for the actual TLS session.[276] This means that the state information (the TLS session ticket) is not as well protected as the TLS session itself. Of particular concern is OpenSSL’s storage of the keys in an application-wide context (SSL_CTX), i.e. for the life of the application, and not allowing for re-keying of the AES128-CBC-SHA256 TLS session tickets without resetting the application-wide OpenSSL context (which is uncommon, error-prone and often requires manual administrative intervention).[277][275]
TLS record
This is the general format of all TLS records.
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
Content type | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..(m−1) |
Protocol message(s) | |||
| Bytes m..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) |
Content type This field identifies the Record Layer Protocol Type contained in this record.
| Hex | Dec | Type |
|---|---|---|
| 0x14 | 20 | ChangeCipherSpec |
| 0x15 | 21 | Alert |
| 0x16 | 22 | Handshake |
| 0x17 | 23 | Application |
| 0x18 | 24 | Heartbeat |
Legacy version This field identifies the major and minor version of TLS prior to TLS 1.3 for the contained message. For a ClientHello message, this need not be the highest version supported by the client. For TLS 1.3 and later, this must to be set 0x0303 and application must send supported versions in an extra message extension block.
| Major version |
Minor version |
Version type |
|---|---|---|
| 3 | 0 | SSL 3.0 |
| 3 | 1 | TLS 1.0 |
| 3 | 2 | TLS 1.1 |
| 3 | 3 | TLS 1.2 |
| 3 | 4 | TLS 1.3 |
Length The length of “protocol message(s)”, “MAC” and “padding” fields combined (i.e. q−5), not to exceed 2 14 bytes (16 KiB). Protocol message(s) One or more messages identified by the Protocol field. Note that this field may be encrypted depending on the state of the connection. MAC and padding A message authentication code computed over the “protocol message(s)” field, with additional key material included. Note that this field may be encrypted, or not included entirely, depending on the state of the connection. No “MAC” or “padding” fields can be present at end of TLS records before all cipher algorithms and parameters have been negotiated and handshaked and then confirmed by sending a CipherStateChange record (see below) for signalling that these parameters will take effect in all further records sent by the same peer. Handshake protocol
Most messages exchanged during the setup of the TLS session are based on this record, unless an error or warning occurs and needs to be signaled by an Alert protocol record (see below), or the encryption mode of the session is modified by another record (see ChangeCipherSpec protocol below).
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
22 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..8 |
Message type | Handshake message data length | ||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||
| Bytes 9..(n−1) |
Handshake message data | |||
| Bytes n..(n+3) |
Message type | Handshake message data length | ||
| (bits 23..16) | (bits 15..8) | (bits 7..0) | ||
| Bytes (n+4).. |
Handshake message data |
Message type This field identifies the handshake message type.
| Code | Description |
|---|---|
| 0 | HelloRequest |
| 1 | ClientHello |
| 2 | ServerHello |
| 4 | NewSessionTicket |
| 8 | EncryptedExtensions (TLS 1.3 only) |
| 11 | Certificate |
| 12 | ServerKeyExchange |
| 13 | CertificateRequest |
| 14 | ServerHelloDone |
| 15 | CertificateVerify |
| 16 | ClientKeyExchange |
| 20 | Finished |
Handshake message data length This is a 3-byte field indicating the length of the handshake data, not including the header.
Note that multiple handshake messages may be combined within one record.
Alert protocol
This record should normally not be sent during normal handshaking or application exchanges. However, this message can be sent at any time during the handshake and up to the closure of the session. If this is used to signal a fatal error, the session will be closed immediately after sending this record, so this record is used to give a reason for this closure. If the alert level is flagged as a warning, the remote can decide to close the session if it decides that the session is not reliable enough for its needs (before doing so, the remote may also send its own signal).
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
21 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | 0 | 2 | |
| Bytes 5..6 |
Level | Description | N/A | |
| Bytes 7..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) |
Level This field identifies the level of alert. If the level is fatal, the sender should close the session immediately. Otherwise, the recipient may decide to terminate the session itself, by sending its own fatal alert and closing the session itself immediately after sending it. The use of Alert records is optional, however if it is missing before the session closure, the session may be resumed automatically (with its handshakes). Normal closure of a session after termination of the transported application should preferably be alerted with at least the Close notify Alert type (with a simple warning level) to prevent such automatic resume of a new session. Signalling explicitly the normal closure of a secure session before effectively closing its transport layer is useful to prevent or detect attacks (like attempts to truncate the securely transported data, if it intrinsically does not have a predetermined length or duration that the recipient of the secured data may expect).
| Code | Level type | Connection state |
|---|---|---|
| 1 | warning | connection or security may be unstable. |
| 2 | fatal | connection or security may be compromised, or an unrecoverable error has occurred. |
Description This field identifies which type of alert is being sent.
| Code | Description | Level types | Note |
|---|---|---|---|
| 0 | Close notify | warning/fatal | |
| 10 | Unexpected message | fatal | |
| 20 | Bad record MAC | fatal | Possibly a bad SSL implementation, or payload has been tampered with e.g. FTP firewall rule on FTPS server. |
| 21 | Decryption failed | fatal | TLS only, reserved |
| 22 | Record overflow | fatal | TLS only |
| 30 | Decompression failure | fatal | |
| 40 | Handshake failure | fatal | |
| 41 | No certificate | warning/fatal | SSL 3.0 only, reserved |
| 42 | Bad certificate | warning/fatal | |
| 43 | Unsupported certificate | warning/fatal | e.g. certificate has only server authentication usage enabled and is presented as a client certificate |
| 44 | Certificate revoked | warning/fatal | |
| 45 | Certificate expired | warning/fatal | Check server certificate expire also check no certificate in the chain presented has expired |
| 46 | Certificate unknown | warning/fatal | |
| 47 | Illegal parameter | fatal | |
| 48 | Unknown CA (Certificate authority) | fatal | TLS only |
| 49 | Access denied | fatal | TLS only – e.g. no client certificate has been presented (TLS: Blank certificate message or SSLv3: No Certificate alert), but server is configured to require one. |
| 50 | Decode error | fatal | TLS only |
| 51 | Decrypt error | warning/fatal | TLS only |
| 60 | Export restriction | fatal | TLS only, reserved |
| 70 | Protocol version | fatal | TLS only |
| 71 | Insufficient security | fatal | TLS only |
| 80 | Internal error | fatal | TLS only |
| 86 | Inappropriate fallback | fatal | TLS only |
| 90 | User canceled | fatal | TLS only |
| 100 | No renegotiation | warning | TLS only |
| 110 | Unsupported extension | warning | TLS only |
| 111 | Certificate unobtainable | warning | TLS only |
| 112 | Unrecognized name | warning/fatal | TLS only; client’s Server Name Indicator specified a hostname not supported by the server |
| 113 | Bad certificate status response | fatal | TLS only |
| 114 | Bad certificate hash value | fatal | TLS only |
| 115 | Unknown PSK identity (used in TLS-PSK and TLS-SRP) | fatal | TLS only |
| 116 | Certificate required | fatal | TLS version 1.3 only |
| 120 or 255 | No application protocol | fatal | TLS version 1.3 only |
ChangeCipherSpec protocol
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
20 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | 0 | 1 | |
| Byte 5 |
CCS protocol type | N/A |
CCS protocol type Currently only 1. Application protocol
| Offset | Byte +0 | Byte +1 | Byte +2 | Byte +3 |
|---|---|---|---|---|
| Byte 0 |
23 | N/A | ||
| Bytes 1..4 |
Legacy version | Length | ||
| (Major) | (Minor) | (bits 15..8) | (bits 7..0) | |
| Bytes 5..(m−1) |
Application data | |||
| Bytes m..(p−1) |
MAC (optional) | |||
| Bytes p..(q−1) |
Padding (block ciphers only) |
Length Length of application data (excluding the protocol header and including the MAC and padding trailers) MAC 32 bytes for the SHA-256-based HMAC, 20 bytes for the SHA-1-based HMAC, 16 bytes for the MD5-based HMAC. Padding Variable length; last byte contains the padding length.
Support for name-based virtual servers
From the application protocol point of view, TLS belongs to a lower layer, although the TCP/IP model is too coarse to show it. This means that the TLS handshake is usually (except in the STARTTLS case) performed before the application protocol can start. In the name-based virtual server feature being provided by the application layer, all co-hosted virtual servers share the same certificate because the server has to select and send a certificate immediately after the ClientHello message. This is a big problem in hosting environments because it means either sharing the same certificate among all customers or using a different IP address for each of them.
There are two known workarounds provided by X.509:
- If all virtual servers belong to the same domain, a wildcard certificate can be used.[286] Besides the loose host name selection that might be a problem or not, there is no common agreement about how to match wildcard certificates. Different rules are applied depending on the application protocol or software used.[287]
- Add every virtual host name in the subjectAltName extension. The major problem being that the certificate needs to be reissued whenever a new virtual server is added.
To provide the server name, RFC 4366 Transport Layer Security (TLS) Extensions allow clients to include a Server Name Indication extension (SNI) in the extended ClientHello message. This extension hints to the server immediately which name the client wishes to connect to, so the server can select the appropriate certificate to send to the clients.
RFC 2817 also documents a method to implement name-based virtual hosting by upgrading HTTP to TLS via an HTTP/1.1 Upgrade header. Normally this is to securely implement HTTP over TLS within the main “http” URI scheme (which avoids forking the URI space and reduces the number of used ports), however, few implementations currently support this.[citation needed]
Standards
Primary standards
The current approved version of TLS is version 1.3, which is specified in:
- RFC 8446: “The Transport Layer Security (TLS) Protocol Version 1.3”.
The current standard replaces these former versions, which are now considered obsolete:
- RFC 2246: “The TLS Protocol Version 1.0”.
- RFC 4346: “The Transport Layer Security (TLS) Protocol Version 1.1”.
- RFC 5246: “The Transport Layer Security (TLS) Protocol Version 1.2”.
As well as the never standardized SSL 2.0 and 3.0, which are considered obsolete:
- Internet Draft (1995), SSL Version 2.0
- RFC 6101: “The Secure Sockets Layer (SSL) Protocol Version 3.0”.
Extensions
Other RFCs subsequently extended TLS.
Extensions to TLS 1.0 include:
- RFC 2595: “Using TLS with IMAP, POP3 and ACAP”. Specifies an extension to the IMAP, POP3 and ACAP services that allow the server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 2712: “Addition of Kerberos Cipher Suites to Transport Layer Security (TLS)”. The 40-bit cipher suites defined in this memo appear only for the purpose of documenting the fact that those cipher suite codes have already been assigned.
- RFC 2817: “Upgrading to TLS Within HTTP/1.1”, explains how to use the Upgrade mechanism in HTTP/1.1 to initiate Transport Layer Security (TLS) over an existing TCP connection. This allows unsecured and secured HTTP traffic to share the same well known port (in this case, http: at 80 rather than https: at 443).
- RFC 2818: “HTTP Over TLS”, distinguishes secured traffic from insecure traffic by the use of a different ‘server port’.
- RFC 3207: “SMTP Service Extension for Secure SMTP over Transport Layer Security”. Specifies an extension to the SMTP service that allows an SMTP server and client to use transport-layer security to provide private, authenticated communication over the Internet.
- RFC 3268: “AES Ciphersuites for TLS”. Adds Advanced Encryption Standard (AES) cipher suites to the previously existing symmetric ciphers.
- RFC 3546: “Transport Layer Security (TLS) Extensions”, adds a mechanism for negotiating protocol extensions during session initialisation and defines some extensions. Made obsolete by RFC 4366.
- RFC 3749: “Transport Layer Security Protocol Compression Methods”, specifies the framework for compression methods and the DEFLATE compression method.
- RFC 3943: “Transport Layer Security (TLS) Protocol Compression Using Lempel-Ziv-Stac (LZS)”.
- RFC 4132: “Addition of Camellia Cipher Suites to Transport Layer Security (TLS)”.
- RFC 4162: “Addition of SEED Cipher Suites to Transport Layer Security (TLS)”.
- RFC 4217: “Securing FTP with TLS”.
- RFC 4279: “Pre-Shared Key Ciphersuites for Transport Layer Security (TLS)”, adds three sets of new cipher suites for the TLS protocol to support authentication based on pre-shared keys.
Extensions to TLS 1.1 include:
- RFC 4347: “Datagram Transport Layer Security” specifies a TLS variant that works over datagram protocols (such as UDP).
- RFC 4366: “Transport Layer Security (TLS) Extensions” describes both a set of specific extensions and a generic extension mechanism.
- RFC 4492: “Elliptic Curve Cryptography (ECC) Cipher Suites for Transport Layer Security (TLS)”.
- RFC 4680: “TLS Handshake Message for Supplemental Data”.
- RFC 4681: “TLS User Mapping Extension”.
- RFC 4785: “Pre-Shared Key (PSK) Ciphersuites with NULL Encryption for Transport Layer Security (TLS)”.
- RFC 5054: “Using the Secure Remote Password (SRP) Protocol for TLS Authentication”. Defines the TLS-SRP ciphersuites.
- RFC 5077: “Transport Layer Security (TLS) Session Resumption without Server-Side State”.
- RFC 5081: “Using OpenPGP Keys for Transport Layer Security (TLS) Authentication”, obsoleted by RFC 6091.
Extensions to TLS 1.2 include:
- RFC 5288: “AES Galois Counter Mode (GCM) Cipher Suites for TLS”.
- RFC 5289: “TLS Elliptic Curve Cipher Suites with SHA-256/384 and AES Galois Counter Mode (GCM)”.
- RFC 5746: “Transport Layer Security (TLS) Renegotiation Indication Extension”.
- RFC 5878: “Transport Layer Security (TLS) Authorization Extensions”.
- RFC 5932: “Camellia Cipher Suites for TLS”
- RFC 6066: “Transport Layer Security (TLS) Extensions: Extension Definitions”, includes Server Name Indication and OCSP stapling.
- RFC 6091: “Using OpenPGP Keys for Transport Layer Security (TLS) Authentication”.
- RFC 6176: “Prohibiting Secure Sockets Layer (SSL) Version 2.0”.
- RFC 6209: “Addition of the ARIA Cipher Suites to Transport Layer Security (TLS)”.
- RFC 6347: “Datagram Transport Layer Security Version 1.2”.
- RFC 6367: “Addition of the Camellia Cipher Suites to Transport Layer Security (TLS)”.
- RFC 6460: “Suite B Profile for Transport Layer Security (TLS)”.
- RFC 6655: “AES-CCM Cipher Suites for Transport Layer Security (TLS)”.
- RFC 7027: “Elliptic Curve Cryptography (ECC) Brainpool Curves for Transport Layer Security (TLS)”.
- RFC 7251: “AES-CCM Elliptic Curve Cryptography (ECC) Cipher Suites for TLS”.
- RFC 7301: “Transport Layer Security (TLS) Application-Layer Protocol Negotiation Extension”.
- RFC 7366: “Encrypt-then-MAC for Transport Layer Security (TLS) and Datagram Transport Layer Security (DTLS)”.
- RFC 7465: “Prohibiting RC4 Cipher Suites”.
- RFC 7507: “TLS Fallback Signaling Cipher Suite Value (SCSV) for Preventing Protocol Downgrade Attacks”.
- RFC 7568: “Deprecating Secure Sockets Layer Version 3.0”.
- RFC 7627: “Transport Layer Security (TLS) Session Hash and Extended Master Secret Extension”.
- RFC 7685: “A Transport Layer Security (TLS) ClientHello Padding Extension”.
Encapsulations of TLS include:
- RFC 5216: “The EAP-TLS Authentication Protocol”
Informational RFCs
- RFC 7457: “Summarizing Known Attacks on Transport Layer Security (TLS) and Datagram TLS (DTLS)”
- RFC 7525: “Recommendations for Secure Use of Transport Layer Security (TLS) and Datagram Transport Layer Security (DTLS)”
See also
- Application-Layer Protocol Negotiation – a TLS extension used for SPDY and TLS False Start
- Bullrun (decryption program) – a secret anti-encryption program run by the U.S. National Security Agency
- Certificate authority
- Certificate Transparency
- HTTP Strict Transport Security – HSTS
- Key ring file
- Private Communications Technology (PCT) – a historic Microsoft competitor to SSL 2.0
- QUIC (Quick UDP Internet Connections) – “…was designed to provide security protection equivalent to TLS/SSL”; QUIC’s main goal is to improve perceived performance of connection-oriented web applications that are currently using TCP
- Server-Gated Cryptography
- tcpcrypt
- DTLS
- TLS acceleration
References
- ^ Lawrence, Scott; Khare, Rohit (May 2000). “Upgrading to TLS Within HTTP/1.1”. tools.ietf.org. Retrieved 15 December 2018.
- ^ “SSL/TLS in Detail”. TechNet. Microsoft Docs. Retrieved 2021-10-24.
- ^ a b Hooper, Howard (2012). CCNP Security VPN 642-648 Official Cert Guide (2 ed.). Cisco Press. p. 22. ISBN 9780132966382.
- ^ a b Spott, Andrew; Leek, Tom; et al. “What layer is TLS?”. Information Security Stack Exchange.
- ^ a b T. Dierks, E. Rescorla (August 2008). “Introduction”. The Transport Layer Security (TLS) Protocol Version 1.2. sec. 1. doi:10.17487/RFC5246. RFC 5246.
- ^ E. Rescorla (August 2008). “The Transport Layer Security (TLS) Protocol Version 1.3”.
- ^ a b c d T. Dierks; E. Rescorla (August 2008). “The Transport Layer Security (TLS) Protocol Version 1.2”. Archived from the original on 2017-12-24.
- ^ a b c d e Bright, Peter (17 October 2018). “Apple, Google, Microsoft, and Mozilla come together to end TLS 1.0”. Retrieved 17 October 2018.
- ^ a b c d “Here is what is new and changed in Firefox 74.0 Stable – gHacks Tech News”. www.ghacks.net. 10 March 2020. Retrieved 2020-03-10.
- ^ a b c d “TLS 1.0 and TLS 1.1 – Chrome Platform Status”. chromestatus.com. Retrieved 2020-03-10.
- ^ “Creating TLS: The Pioneering Role of Ruth Nelson”.
- ^ Thomas Y. C. Woo, Raghuram Bindignavle, Shaowen Su and Simon S. Lam, SNP: An interface for secure network programming Proceedings USENIX Summer Technical Conference, June 1994
- ^ Messmer, Ellen. “Father of SSL, Dr. Taher Elgamal, Finds Fast-Moving IT Projects in the Middle East”. Network World. Archived from the original on 31 May 2014. Retrieved 30 May 2014.
- ^ Greene, Tim. “Father of SSL says despite attacks, the security linchpin has lots of life left”. Network World. Archived from the original on 31 May 2014. Retrieved 30 May 2014.
- ^ a b Oppliger, Rolf (2016). “Introduction”. SSL and TLS: Theory and Practice (2nd ed.). Artech House. p. 13. ISBN 978-1-60807-999-5. Retrieved 2018-03-01 – via Google Books.
- ^ “THE SSL PROTOCOL”. Netscape Corporation. 2007. Archived from the original on 14 June 1997.
- ^ Rescorla 2001
- ^ “POODLE: SSLv3 vulnerability (CVE-2014-3566)”. Archived from the original on 5 December 2014. Retrieved 21 October 2014.
- ^ “Security Standards and Name Changes in the Browser Wars”. Retrieved 2020-02-29.
- ^ Laura K. Gray (2015-12-18). “Date Change for Migrating from SSL and Early TLS”. Payment Card Industry Security Standards Council blog. Retrieved 2018-04-05.
- ^ Company, Newtek – Your Business Solutions. “Changes to PCI Compliance are Coming June 30. Is Your Ecommerce Business Ready?”. Forbes. Retrieved 2018-06-20.
- ^ Dierks, T. & E. Rescorla (April 2006). “The Transport Layer Security (TLS) Protocol Version 1.1”. RFC 4346. Archived from the original on 2017-12-24.
- ^ a b Polk, Tim; McKay, Terry; Chokhani, Santosh (April 2014). “Guidelines for the Selection, Configuration, and Use of Transport Layer Security (TLS) Implementations” (PDF). National Institute of Standards and Technology. p. 67. Archived from the original (PDF) on 2014-05-08. Retrieved 2014-05-07.{{cite web}}: CS1 maint: uses authors parameter (link)
- ^ “Twitter will deprecate support for TLS 1.0, TLS 1.1 on July 15”. Hashed Out by The SSL Store. 2019-07-12. Retrieved 14 June 2021.
- ^ Mackie, Kurt. “Microsoft Delays End of Support for TLS 1.0 and 1.1 -“. Microsoft Certified Professional Magazine Online.
- ^ “TLS 1.2 FAQ – Knowledge Base”. Answers.psionline.com. Retrieved 20 February 2022.
- ^ T. Dierks, E. Rescorla (August 2008). “Finished”. The Transport Layer Security (TLS) Protocol Version 1.2. sec. 7.4.9. doi:10.17487/RFC5246. RFC 5246.
- ^ “Differences between TLS 1.2 and TLS 1.3 (#TLS13)”. WolfSSL. 18 September 2019. Archived from the original on 19 September 2019. Retrieved 18 September 2019.
- ^ “NSS 3.29 release notes”. Mozilla Developer Network. February 2017. Archived from the original on 2017-02-22.
- ^ “Enable TLS 1.3 by default”. Bugzilla@Mozilla. 16 October 2016. Retrieved 10 October 2017.
- ^ “Firefox — Notes (60.0)”. Mozilla. Retrieved 2018-05-10.
- ^ “ProxySG, ASG and WSS will interrupt SSL connections when clients using TLS 1.3 access sites also using TLS 1.3”. BlueTouch Online. 16 May 2017. Archived from the original on 12 September 2017. Retrieved 11 September 2017.
- ^ “TLS 1.3 IETF 100 Hackathon”. Archived from the original on 2018-01-15.
- ^ a b IETF – Internet Engineering Task Force (2017-11-12), IETF Hackathon Presentations and Awards, archived from the original on 2021-10-28, retrieved 2017-11-14
- ^ “Hurrah! TLS 1.3 is here. Now to implement it and put it into software”. Retrieved 2018-03-28.
- ^ IETF – Internet Engineering Task Force (2018-07-15), IETF102-HACKATHON-20180715-1400, archived from the original on 2021-10-28, retrieved 2018-07-18
- ^ “wolfSSL TLS 1.3 BETA Release Now Available”. info@wolfssl.com. 11 May 2017. Retrieved 11 May 2017.
- ^ “TLS 1.3 PROTOCOL SUPPORT”. info@wolfssl.com.
- ^ “TLS 1.3 Draft 28 Support in wolfSSL”. info@wolfssl.com. 14 June 2018. Retrieved 14 June 2018.
- ^ “OpenSSL 1.1.1 Is Released”. Matt Caswell. 11 Sep 2018. Retrieved 19 Dec 2018.
- ^ “Protocols in TLS/SSL (Schannel SSP)”. Microsoft Docs. Retrieved 24 November 2021.
- ^ Hoffman-Andrews, Jacob (2019-02-26). “ETS Isn’t TLS and You Shouldn’t Use It”. Electronic Frontier Foundation. Retrieved 2019-02-27.
- ^ TS 103 523-3 – V1.1.1 – CYBER; Middlebox Security Protocol; Part 3: Profile for enterprise network and data centre access control ETSI
- ^ A finance industry group is pushing an intentionally broken cryptography “standard” called ETS Boing Boing
- ^ Rea, Scott (2013). “Alternatives to Certification Authorities for a Secure Web” (PDF). RSA Conference Asia Pacific. Archived (PDF) from the original on 7 October 2016. Retrieved 7 September 2016.
- ^ “Counting SSL certificates”. Archived from the original on 16 May 2015. Retrieved 20 February 2022.
- ^ Raymond, Art (3 August 2017). “Lehi’s DigiCert swallows web security competitor in $1 billion deal”. Deseret News. Retrieved 21 May 2020.
- ^ “Market share trends for SSL certificate authorities”. W3Techs. Retrieved 21 May 2020.
- ^ Law Enforcement Appliance Subverts SSL Archived 2014-03-15 at the Wayback Machine, Wired, 2010-04-03.
- ^ New Research Suggests That Governments May Fake SSL Certificates Archived 2016-01-04 at the Wayback Machine, EFF, 2010-03-24.
- ^ P. Eronen, Ed. (December 2005). “Pre-Shared Key Ciphersuites for Transport Layer Security (TLS)”. Internet Engineering Task Force. RFC 4279. Archived from the original on 5 September 2013. Retrieved 9 September 2013. {{cite journal}}: Cite journal requires |journal= (help)
- ^ D. Taylor, Ed. (November 2007). “Using the Secure Remote Password (SRP) Protocol for TLS Authentication”. Internet Engineering Task Force. RFC 5054. Archived from the original on December 7, 2014. Retrieved December 21, 2014. {{cite journal}}: Cite journal requires |journal= (help)
- ^ Gothard, Peter (31 July 2013). “Google updates SSL certificates to 2048-bit encryption”. Computing. Incisive Media. Archived from the original on 22 September 2013. Retrieved 9 September 2013.
- ^ “The value of 2,048-bit encryption: Why encryption key length matters”. SearchSecurity. Archived from the original on 2018-01-16. Retrieved 2017-12-18.
- ^ Sean Turner (September 17, 2015). “Consensus: remove DSA from TLS 1.3”. Archived from the original on October 3, 2015.
- ^ RFC 8422
- ^ a b c d draft-chudov-cryptopro-cptls-04 – GOST 28147-89 Cipher Suites for Transport Layer Security (TLS)
- ^ RFC 5288, 5289
- ^ RFC 6655, 7251
- ^ RFC 6367
- ^ RFC 5932, 6367
- ^ a b RFC 6209
- ^ RFC 4162
- ^ “On the Practical (In-)Security of 64-bit Block Ciphers — Collision Attacks on HTTP over TLS and OpenVPN” (PDF). 2016-10-28. Archived (PDF) from the original on 2017-04-24. Retrieved 2017-06-08.
- ^ “NIST Special Publication 800-57 Recommendation for Key Management — Part 1: General (Revised)” (PDF). 2007-03-08. Archived from the original (PDF) on June 6, 2014. Retrieved 2014-07-03.
- ^ a b c Qualys SSL Labs. “SSL/TLS Deployment Best Practices”. Archived from the original on 4 July 2015. Retrieved 2 June 2015.
- ^ RFC 5469
- ^ RFC 7905
- ^ “RFC 5246 – The Transport Layer Security (TLS) Protocol Version 1.2”. Datatracker.ietf.org. Retrieved 20 February 2022.
- ^ “Http vs https”. Archived from the original on 2015-02-12. Retrieved 2015-02-12.
- ^ a b c d As of October 17, 2021. “SSL Pulse: Survey of the SSL Implementation of the Most Popular Websites”. Qualys. Retrieved 2021-11-09.
- ^ a b ivanr (19 March 2013). “RC4 in TLS is Broken: Now What?”. Qualsys Security Labs. Archived from the original on 2013-08-27. Retrieved 2013-07-30.
- ^ a b c Bodo Möller, Thai Duong & Krzysztof Kotowicz. “This POODLE Bites: Exploiting The SSL 3.0 Fallback” (PDF). Archived (PDF) from the original on 2014-10-14. Retrieved 2014-10-15.
- ^ “What browsers support Extended Validation (EV) and display an EV indicator?”. Symantec. Archived from the original on 2015-12-31. Retrieved 2014-07-28.
- ^ a b c d e f g h i j “SHA-256 Compatibility”. Archived from the original on 2015-07-01. Retrieved 2015-06-12.
- ^ a b c d e f g h i j k l m n o p q r s “ECC Compatibility”. Archived from the original on 2016-02-17. Retrieved 2015-06-13.
- ^ a b “Tracking the FREAK Attack”. Archived from the original on 2015-03-06. Retrieved 2015-03-08.
- ^ a b “FREAK: Factoring RSA Export Keys”. Archived from the original on 2015-03-11. Retrieved 2015-03-08.
- ^ “Dev Channel Update”. 2012-05-29. Archived from the original on 2013-03-02. Retrieved 2011-06-01.
- ^ “Stable Channel Update”. 2012-08-21. Archived from the original on 2012-08-25. Retrieved 2012-08-22.
- ^ Chromium Project (2013-05-30). “Chromium TLS 1.2 Implementation”.
- ^ “The Chromium Project: BoringSSL”. Archived from the original on 2015-09-23. Retrieved 2015-09-05.
- ^ a b “Chrome Stable Release”. Chrome Releases. 2011-10-25. Archived from the original on 2015-02-20. Retrieved 2015-02-01.
- ^ “SVN revision log on Chrome 10.0.648.127 release”. Archived from the original on 2014-06-19. Retrieved 2014-06-19.
- ^ a b “ImperialViolet – CRIME”. 2012-09-22. Archived from the original on 2015-01-10. Retrieved 2014-10-18.
- ^ a b “SSL/TLS Overview”. 2008-08-06. Archived from the original on 2013-07-03. Retrieved 2013-03-29.
- ^ a b “Chromium Issue 90392”. 2008-08-06. Archived from the original on 2013-08-03. Retrieved 2013-06-28.
- ^ a b “Issue 23503030 Merge 219882”. 2013-09-03. Archived from the original on 2014-02-26. Retrieved 2013-09-19.
- ^ a b “Issue 278370: Unable to submit client certificates over TLS 1.2 from Windows”. 2013-08-23. Archived from the original on 2013-10-05. Retrieved 2013-10-03.
- ^ Möller, Bodo (2014-10-14). “This POODLE bites: exploiting the SSL 3.0 fallback”. Google Online Security blog. Google (via Blogspot). Archived from the original on 2014-10-28. Retrieved 2014-10-28.
- ^ a b c “An update on SSLv3 in Chrome”. Security-dev. 2014-10-31. Retrieved 2014-11-04.
- ^ “Stable Channel Update”. Mozilla Developer Network. 2014-02-20. Archived from the original on 2014-10-24. Retrieved 2014-11-14.
- ^ “Changelog for Chrome 33.0.1750.117”. Google. Archived from the original on 2014-01-16. Retrieved 2014-11-14.
- ^ “Issue 318442: Update to NSS 3.15.3 and NSPR 4.10.2”. Archived from the original on 2015-03-15. Retrieved 2014-11-14.
- ^ a b “Issue 693963003: Add minimum TLS version control to about:flags and Finch gate it. – Code Review”. Archived from the original on 2015-04-16. Retrieved 2015-01-22.
- ^ “Issue 375342: Drop RC4 Support”. Archived from the original on 2015-09-12. Retrieved 2015-05-22.
- ^ “Issue 436391: Add info on end of life of SSLVersionFallbackMin & SSLVersionMin policy in documentation”. Archived from the original on 2015-04-18. Retrieved 2015-04-19.
- ^ “Issue 490240: Increase minimum DH size to 1024 bits (tracking bug)”. Archived from the original on 2015-09-12. Retrieved 2015-05-29.
- ^ a b c d e f g “Intent to deprecate: RC4”. Retrieved 2015-12-21.
- ^ a b c d e f g “An update on SHA-1 certificates in Chrome”. 2015-12-18. Archived from the original on 2015-12-18. Retrieved 2015-12-21.
- ^ a b “Chrome Enterprise release notes – Google Chrome Enterprise Help”.
- ^ a b “Microsoft Edge Browser Policy Documentation | Microsoft Docs”. Docs.microsoft.com. 2021-10-15. Retrieved 2022-02-15.
- ^ a b c d “Security in Firefox 2”. 2008-08-06. Archived from the original on 2014-07-14. Retrieved 2009-03-31.
- ^ a b “Attack against TLS-protected communications”. Mozilla Security Blog. Mozilla. 2011-09-27. Archived from the original on 2015-03-04. Retrieved 2015-02-01.
- ^ a b “Introduction to SSL”. MDN. Archived from the original on 2014-07-14. Retrieved 2014-06-19.
- ^ a b “NSS 3.15.3 Release Notes”. Mozilla Developer Network. Mozilla. Archived from the original on 2014-06-05. Retrieved 2014-07-13.
- ^ a b “MFSA 2013-103: Miscellaneous Network Security Services (NSS) vulnerabilities”. Mozilla. Mozilla. Archived from the original on 2014-07-14. Retrieved 2014-07-13.
- ^ “Bug 565047 – (RFC4346) Implement TLS 1.1 (RFC 4346)”. Retrieved 2013-10-29.
- ^ “Bug 480514 – Implement support for TLS 1.2 (RFC 5246)”. Retrieved 2013-10-29.
- ^ “Bug 733647 – Implement TLS 1.1 (RFC 4346) in Gecko (Firefox, Thunderbird), on by default”. Retrieved 2013-12-04.
- ^ a b “Firefox Notes – Desktop”. 2014-02-04. Archived from the original on 2014-02-07. Retrieved 2014-02-04.
- ^ “Bug 861266 – Implement TLS 1.2 (RFC 5246) in Gecko (Firefox, Thunderbird), on by default”. Retrieved 2013-11-18.
- ^ a b c “The POODLE Attack and the End of SSL 3.0”. Mozilla blog. Mozilla. 2014-10-14. Archived from the original on 2014-10-18. Retrieved 2014-10-28.
- ^ “Firefox — Notes (34.0) — Mozilla”. mozilla.org. 2014-12-01. Archived from the original on 2015-04-09. Retrieved 2015-04-03.
- ^ “Bug 1083058 – A pref to control TLS version fallback”. bugzilla.mozilla.org. Retrieved 2014-11-06.
- ^ “Bug 1036737 – Add support for draft-ietf-tls-downgrade-scsv to Gecko/Firefox”. bugzilla.mozilla.org. Retrieved 2014-10-29.
- ^ a b c “Bug 1166031 – Update to NSS 3.19.1”. bugzilla.mozilla.org. Retrieved 2015-05-29.
- ^ “Bug 1088915 – Stop offering RC4 in the first handshakes”. bugzilla.mozilla.org. Retrieved 2014-11-04.
- ^ “Firefox — Notes (39.0) — Mozilla”. mozilla.org. 2015-06-30. Archived from the original on 2015-07-03. Retrieved 2015-07-03.
- ^ “Google, Microsoft, and Mozilla will drop RC4 encryption in Chrome, Edge, IE, and Firefox next year”. VentureBeat. 2015-09-01. Archived from the original on 2015-09-05. Retrieved 2015-09-05.
- ^ “Intent to ship: RC4 disabled by default in Firefox 44”. Archived from the original on 2011-01-22. Retrieved 2015-10-18.
- ^ “RC4 is now allowed only on whitelisted sites (Reverted)”. Retrieved 2015-11-02.
- ^ “Firefox — Notes (44.0) — Mozilla”. mozilla.org. 2016-01-26. Archived from the original on 2016-03-04. Retrieved 2016-03-09.
- ^ “Bug 1342082 – Disable TLS 1.3 for FF52 Release”. Retrieved 2017-03-29.
- ^ a b “Firefox 78.0, See All New Features, Updates and Fixes”.
- ^ Microsoft (2012-09-05). “Secure Channel”. Archived from the original on 2012-08-29. Retrieved 2012-10-18.
- ^ Microsoft (2009-02-27). “MS-TLSP Appendix A”. Archived from the original on 2013-09-27. Retrieved 2009-03-19.
- ^ a b “What browsers only support SSLv2?”. Retrieved 2014-06-19.
- ^ a b c d “SHA2 and Windows – Windows PKI blog – Site Home – TechNet Blogs”. 2010-09-30. Archived from the original on 2014-07-16. Retrieved 2014-07-29.
- ^ a b c d e “HTTPS Security Improvements in Internet Explorer 7”. Archived from the original on 2013-10-10. Retrieved 2013-10-29.
- ^ “TLS Cipher Suites”. Microsoft. Archived from the original on 2017-03-13.
- ^ “Cipher Suites in TLS/SSL (Schannel SSP) – Win32 apps”. Archived from the original on 2015-03-11. Retrieved 2017-07-19.
- ^ a b c d e f g MSRC (2015-03-10). Vulnerability in Schannel Could Allow Security Feature Bypass (3046049). Security Bulletins (Technical report). MS15-031. Retrieved 2021-10-24 – via Microsoft Docs.
- ^ a b c d e f g MSRC (2015-05-12). Vulnerability in Schannel Could Allow Information Disclosure (3061518). Security Bulletins (Technical report). MS15-055. Retrieved 2021-10-24 – via Microsoft Docs.
- ^ a b c d “Update to add support for TLS 1.1 and TLS 1.2 in Windows Server 2008 SP2, Windows Embedded POSReady 2009, and Windows Embedded Standard 2009”. Retrieved 2017-07-19.
- ^ a b “Windows 7 adds support for TLSv1.1 and TLSv1.2 – IEInternals – Site Home – MSDN Blogs”. Archived from the original on 2013-12-26. Retrieved 2013-10-29.
- ^ Thomlinson, Matt (2014-11-11). “Hundreds of Millions of Microsoft Customers Now Benefit from Best-in-Class Encryption”. Microsoft Security. Archived from the original on 2014-11-14. Retrieved 2014-11-14.
- ^ “Microsoft security advisory: Update for disabling RC4”. Support.microsoft.com. Archived from the original on 11 March 2015. Retrieved 20 February 2022.
- ^ a b c d Microsoft (2013-09-24). “IE11 Changes”. Archived from the original on 2013-10-30. Retrieved 2013-11-01.
- ^ “February 2015 security updates for Internet Explorer”. 2015-02-11. Archived from the original on 2015-02-11. Retrieved 2015-02-11.
- ^ “Update turns on the setting to disable SSL 3.0 fallback for protected mode sites by default in Internet Explorer 11”. Archived from the original on 2015-02-14. Retrieved 2015-02-11.
- ^ MSRC (2014-10-14). Vulnerability in SSL 3.0 Could Allow Information Disclosure. Security Advisories (Technical report). 3009008. Retrieved 2021-10-24 – via Microsoft Docs.
- ^ Microsoft Edge Team (2016-08-09). “RC4 is now disabled in Microsoft Edge and Internet Explorer 11”. Microsoft. Archived from the original on 2016-08-21.
- ^ “Internet Explorer 11 for Windows Server 2012 and Windows Embedded 8 Standard”. Microsoft Support. 2019-04-16.
- ^ a b c d e “TLS (Schannel SSP) changes in Windows 10 and Windows Server 2016”. Windows Server. Microsoft Docs. Retrieved 2021-10-24.
- ^ a b “Protocols in TLS/SSL (Schannel SSP) – Win32 apps”. Docs.microsoft.com. Retrieved 20 February 2022.
- ^ a b c d “What browsers work with Universal SSL”. Archived from the original on 2016-03-04. Retrieved 2015-06-15.
- ^ “POODLE SSL vulnerability – secure your Windo… – Windows Phone 8 Development and Hacking”. XDA Developers. Archived from the original on 2016-09-23.
- ^ a b “What TLS version is used in Windows Phone 8 for secure HTTP connections?”. Microsoft. Archived from the original on 2016-03-04. Retrieved 2014-11-07.
- ^ “Qualys SSL Labs – Projects / User Agent Capabilities: Unknown”. Archived from the original on 2017-03-01.
- ^ a b “Platform Security”. TechNet. Microsoft Docs. 2014-06-25. Retrieved 2021-10-24.
- ^ “Release Notes: Important Issues in Windows 8.1 Preview”. TechNet. Microsoft Docs. 2013-06-24. Retrieved 2021-10-24.
- ^ “W8.1(IE11) vs RC4”. Qualys Community. Archived from the original on 2014-11-04. Retrieved 2014-11-04.
- ^ Adrian, Dimcev. “Common browsers/libraries/servers and the associated cipher suites implemented”. TLS Cipher Suites Project. Archived from the original on 2013-04-17.
- ^ “Features”. Safari. Apple. 2009-06-10. Archived from the original on 2013-04-17. Retrieved 2009-06-10.
- ^ “Curl: Patch to add TLS 1.1 and 1.2 support & replace deprecated functions in SecureTransport”. Sweden: haxx.se. Archived from the original on 2017-03-01.
- ^ Qualys SSL Report: google.co.uk Archived 2017-03-20 at the Wayback Machine (simulation Safari 5.1.9 TLS 1.0)
- ^ “Apple Secures Mac OS X with Mavericks Release”. eSecurity Planet. 2013-10-25. Archived from the original on 2014-07-08. Retrieved 2014-06-23.
- ^ Ristic, Ivan (2013-09-10). “Is BEAST Still a Threat?”. Qualys. Archived from the original on 2014-10-12.
- ^ a b Ristić, Ivan (2013-10-31). “Apple enabled BEAST mitigations in OS X 10.9 Mavericks”. Archived from the original on 2013-11-07. Retrieved 2013-11-07.
- ^ Ristić, Ivan (2014-02-26). “Apple finally releases patch for BEAST”. Qualys. Archived from the original on 2014-07-14. Retrieved 2014-07-01.
- ^ “About Security Update 2014-005”. Apple Support knowledge base article. Apple. Archived from the original on 2014-10-24.
- ^ “About the security content of iOS 8.1”. Apple Support knowledge base article. Apple. Archived from the original on 2014-10-23.
- ^ a b c “About Security Update 2015-002”. Apple Support knowledge base article. Apple. Archived from the original on 2015-03-16. Retrieved 2015-03-09.
- ^ a b “About the security content of OS X Mavericks v10.9”. Archived from the original on 2014-07-04. Retrieved 2014-06-20.
- ^ “User Agent Capabilities: Safari 8 / OS X 10.10”. Qualys SSL Labs. Archived from the original on 2015-09-06. Retrieved 2015-03-07.
- ^ “About the security content of OS X Yosemite v10.10.4 and Security Update 2015-005”. Archived from the original on 2015-07-02. Retrieved 2015-07-03.
- ^ a b Pauly, Tommy (2019-01-29). “TLS 1.3 in iOS”. tls@ietf.org (Mailing list).
- ^ a b c “Technical Note TN2287 – iOS 5 and TLS 1.2 Interoperability Issues”. Apple. 2011-10-14. Archived from the original on 2011-09-07. Retrieved 2012-12-10.
- ^ Liebowitz, Matt (2011-10-13). “Apple issues huge software security patches”. NBC News. Retrieved 2012-12-10.
- ^ MWR Info Security (2012-04-16). “Adventures with iOS UIWebviews”. Archived from the original on 2013-04-17. Retrieved 2012-12-10., section “HTTPS (SSL/TLS)”
- ^ “Secure Transport Reference”. Archived from the original on 2014-06-04. Retrieved 2014-06-23. kSSLProtocol2 is deprecated in iOS
- ^ “iPhone 3.0: Mobile Safari Gets Enhanced Security Certificate Visualization”. The iPhone Blog. 2009-03-31. Archived from the original on 2009-04-03.
- ^ “Projects / User Agent Capabilities: Safari 7 / iOS 7.1”. Qualys SSL Labs. Archived from the original on 2017-03-13.
- ^ “SOAP Request fails randomly on one Server but works on another on iOS7”. Stack Overflow. 2013-10-11. Retrieved 2014-01-05.
- ^ “User Agent Capabilities: Safari 8 / iOS 8.1.2”. Qualys SSL Labs. Archived from the original on 2016-03-04. Retrieved 2015-03-07.
- ^ “About the security content of iOS 8.2”. Apple Support knowledge base article. Apple. Archived from the original on 2015-03-09. Retrieved 2015-03-09.
- ^ “About the security content of iOS 8.4”. Archived from the original on 2015-07-03. Retrieved 2015-07-03.
- ^ “SSLSocket | Android Developers”. Archived from the original on 2015-03-18. Retrieved 2015-03-11.
- ^ a b c d “SSLSocket | Android Developers”. Archived from the original on 2016-03-04. Retrieved 2015-12-17.
- ^ a b “Android 5.0 Behavior Changes | Android Developers”. Archived from the original on 2015-03-09. Retrieved 2015-03-11.
- ^ “Android 8.0 Behavior Changes”. Archived from the original on 2017-12-01.
- ^ “Java Secure Socket Extension (JSSE) Reference Guide”. Oracle Help Center. Retrieved 2021-12-24.
- ^ “Version 1.11.13, 2015-01-11 — Botan”. 2015-01-11. Archived from the original on 2015-01-09. Retrieved 2015-01-16.
- ^ “[gnutls-devel] GnuTLS 3.4.0 released”. 2015-04-08. Archived from the original on 2015-04-16. Retrieved 2015-04-16.
- ^ “[gnutls-devel] gnutls 3.6.4”. 2018-09-24. Retrieved 2020-05-18.
- ^ “Java SE Development Kit 8, Update 31 Release Notes”. Archived from the original on 2015-01-21. Retrieved 2015-01-22.
- ^ a b “8256490: Release Note: Disable TLS 1.0 and 1.1”. JDK Bug System (JBS). OpenJDK. Retrieved 5 January 2022.
- ^ “OpenBSD 5.6 Released”. 2014-11-01. Retrieved 2015-01-20.
- ^ “LibreSSL 2.3.0 Released”. 2015-09-23. Retrieved 2015-09-24.
- ^ “We have released LibreSSL 3.2.2, which will be arriving in the LibreSSL directory of your local OpenBSD mirror soon” (TXT). Ftp.openbsd.org. Retrieved 2022-02-20.
- ^ “Add support for TLS 1.3 ¡ Issue #228 ¡ libressl-portable/portable ¡ GitHub”. Github.com. Retrieved 2022-02-15.
- ^ “MatrixSSL – News”. Archived from the original on 2015-02-14. Retrieved 2014-11-09.
- ^ “mbed TLS 2.0.0 released”. 2015-07-10. Archived from the original on 2015-09-25. Retrieved 2015-07-14.
- ^ “NSS 3.19 release notes”. Mozilla Developer Network. Mozilla. Archived from the original on 2015-06-05. Retrieved 2015-05-06.
- ^ “NSS 3.14 release notes”. Mozilla Developer Network. Mozilla. Archived from the original on 2013-01-17. Retrieved 2012-10-27.
- ^ “NSS 3.15.1 release notes”. Mozilla Developer Network. Mozilla. Archived from the original on 2013-09-22. Retrieved 2013-08-10.
- ^ “NSS 3.39 release notes”. 2018-08-31. Retrieved 2018-09-14.
- ^ “OpenSSL 1.1.0 Series Release Notes”. Archived from the original on 2016-08-25. Retrieved 2016-10-02.
- ^ a b “Major changes between OpenSSL 1.0.0h and OpenSSL 1.0.1 [14 Mar 2012]”. 2012-03-14. Archived from the original on January 20, 2015. Retrieved 2015-01-20.
- ^ “OpenSSL 1.1.1 Is Released”. 2018-09-11. Retrieved 2018-09-14.
- ^ “TLS cipher suites in Microsoft Windows XP and 2003”. Archived from the original on 18 January 2015. Retrieved 20 February 2022.
- ^ a b “SChannel Cipher Suites in Microsoft Windows Vista”. Archived from the original on 12 January 2015. Retrieved 20 February 2022.
- ^ a b c “TLS Cipher Suites in SChannel for Windows 7, 2008R2, 8, 2012”. Archived from the original on 19 March 2015. Retrieved 20 February 2022.
- ^ “Microsoft TLS 1.3 Support Reference”. Microsoft. 2020-01-30. Retrieved 2021-01-01. “What’s new in Windows 10, version 1909 for IT Pros”. Microsoft. 2020-10-03. Retrieved 2021-01-01.
- ^ “Protocols in TLS/SSL (Schannel SSP)”. Microsoft. 2020-12-17. Retrieved 2021-01-01.
- ^ “Protocols in TLS/SSL (Schannel SSP)”. Microsoft. Retrieved 2021-01-01.
- ^ “[wolfssl] wolfSSL 3.6.6 Released”. 2015-08-20. Archived from the original on 2015-10-17. Retrieved 2015-08-25.
- ^ “TLS 1.3 Protocol Support”. Retrieved 2021-05-15.
- ^ “NSS 3.24 release notes”. Mozilla Developer Network. Mozilla. Archived from the original on 2016-08-26. Retrieved 2016-06-19.
- ^ “Technical Note TN2287: iOS 5 and TLS 1.2 Interoperability Issues”. iOS Developer Library. Apple Inc. Archived from the original on 2015-04-03. Retrieved 2012-05-03.
- ^ “Qualys SSL Labs – Projects / User Agent Capabilities”. Archived from the original on 19 September 2015. Retrieved 20 February 2022.
- ^ Georgiev, Martin and Iyengar, Subodh and Jana, Suman and Anubhai, Rishita and Boneh, Dan and Shmatikov, Vitaly (2012). The most dangerous code in the world: validating SSL certificates in non-browser software. Proceedings of the 2012 ACM conference on Computer and communications security (PDF). pp. 38–49. ISBN 978-1-4503-1651-4. Archived (PDF) from the original on 2017-10-22.{{cite book}}: CS1 maint: multiple names: authors list (link)
- ^ “The Use of the SIPS URI Scheme in the Session Initiation Protocol (SIP)”. RFC 5630.
- ^ “Summarizing Known Attacks on Transport Layer Security (TLS) and Datagram TLS (DTLS)”. RFC 7457. Archived from the original on 2016-03-04.
- ^ “CVE – CVE-2009-3555”. Archived from the original on 2016-01-04.
- ^ Eric Rescorla (2009-11-05). “Understanding the TLS Renegotiation Attack”. Educated Guesswork. Archived from the original on 2012-02-09. Retrieved 2009-11-27.
- ^ “SSL_CTX_set_options SECURE_RENEGOTIATION”. OpenSSL Docs. 2010-02-25. Archived from the original on 2010-11-26. Retrieved 2010-11-18.
- ^ “GnuTLS 2.10.0 released”. GnuTLS release notes. 2010-06-25. Archived from the original on 2012-02-09. Retrieved 2011-07-24.
- ^ “NSS 3.12.6 release notes”. NSS release notes. 2010-03-03. Archived from the original on March 6, 2012. Retrieved 2011-07-24.
- ^ A. Langley; N. Modadugu; B. Moeller (2010-06-02). “Transport Layer Security (TLS) False Start”. Internet Engineering Task Force. IETF. Archived from the original on 2013-09-05. Retrieved 2013-07-31.
- ^ Gruener, Wolfgang. “False Start: Google Proposes Faster Web, Chrome Supports It Already”. Archived from the original on 2010-10-07. Retrieved 2011-03-09.
- ^ Smith, Brian. “Limited rollback attacks in False Start and Snap Start”. Archived from the original on 2011-05-04. Retrieved 2011-03-09.
- ^ Dimcev, Adrian. “False Start”. Random SSL/TLS 101. Archived from the original on 2011-05-04. Retrieved 2011-03-09.
- ^ Mavrogiannopoulos, Nikos; Vercautern, Frederik; Velichkov, Vesselin; Preneel, Bart (2012). A cross-protocol attack on the TLS protocol. Proceedings of the 2012 ACM conference on Computer and communications security (PDF). pp. 62–72. ISBN 978-1-4503-1651-4. Archived (PDF) from the original on 2015-07-06.
- ^ “SMACK: State Machine AttaCKs”. Archived from the original on 2015-03-12.
- ^ Goodin, Dan (2015-05-20). “HTTPS-crippling attack threatens tens of thousands of Web and mail servers”. Ars Technica. Archived from the original on 2017-05-19.
- ^ Leyden, John (1 March 2016). “One-third of all HTTPS websites open to DROWN attack”. The Register. Archived from the original on 1 March 2016. Retrieved 2016-03-02.
- ^ a b “More than 11 million HTTPS websites imperiled by new decryption attack”. Ars Technica. March 2016. Archived from the original on 2016-03-01. Retrieved 2016-03-02.
- ^ Thai Duong & Juliano Rizzo (2011-05-13). “Here Come The ⊕ Ninjas”. Archived from the original on 2014-06-03.
- ^ Dan Goodin (2011-09-19). “Hackers break SSL encryption used by millions of sites”. The Register. Archived from the original on 2012-02-09.
- ^ “Y Combinator comments on the issue”. 2011-09-20. Archived from the original on 2013-04-17.
- ^ “Security of CBC Ciphersuites in SSL/TLS: Problems and Countermeasures”. 2004-05-20. Archived from the original on 2012-06-30.
- ^ Ristic, Ivan (Sep 10, 2013). “Is BEAST Still a Threat?”. Archived from the original on 12 October 2014. Retrieved 8 October 2014.
- ^ Brian Smith (2011-09-30). “(CVE-2011-3389) Rizzo/Duong chosen plaintext attack (BEAST) on SSL/TLS 1.0 (facilitated by websockets -76)”.
- ^ MSRC (2012-01-10). Vulnerability in SSL/TLS Could Allow Information Disclosure (2643584). Security Bulletins (Technical report). MS12-006. Retrieved 2021-10-24 – via Microsoft Docs.
- ^ Ristic, Ivan (Oct 31, 2013). “Apple Enabled BEAST Mitigations in OS X 10.9 Mavericks”. Archived from the original on 12 October 2014. Retrieved 8 October 2014.
- ^ Dan Goodin (2012-09-13). “Crack in Internet’s foundation of trust allows HTTPS session hijacking”. Ars Technica. Archived from the original on 2013-08-01. Retrieved 2013-07-31.
- ^ Dennis Fisher (September 13, 2012). “CRIME Attack Uses Compression Ratio of TLS Requests as Side Channel to Hijack Secure Sessions”. ThreatPost. Archived from the original on September 15, 2012. Retrieved 2012-09-13.
- ^ a b Goodin, Dan (1 August 2013). “Gone in 30 seconds: New attack plucks secrets from HTTPS-protected pages”. Ars Technica. Condé Nast. Archived from the original on 3 August 2013. Retrieved 2 August 2013.
- ^ Leyden, John (2 August 2013). “Step into the BREACH: New attack developed to read encrypted web data”. The Register. Archived from the original on 5 August 2013. Retrieved 2 August 2013.
- ^ P. Gutmann (September 2014). “Encrypt-then-MAC for Transport Layer Security (TLS) and Datagram Transport Layer Security (DTLS)”. Archived from the original on 2015-05-12. {{cite journal}}: Cite journal requires |journal= (help)
- ^ Langley, Adam (December 8, 2014). “The POODLE bites again”. Archived from the original on December 8, 2014. Retrieved 2014-12-08.
- ^ “ssl – Safest ciphers to use with the BEAST? (TLS 1.0 exploit) I’ve read that RC4 is immune”. Serverfault.com. Retrieved 20 February 2022.
- ^ Pouyan Sepehrdad; Serge Vaudenay; Martin Vuagnoux (2011). “Discovery and Exploitation of New Biases in RC4”. In Alex Biryukov; Guang Gong; Douglas R. Stinson (eds.). Selected Areas in Cryptography: 17th International Workshop, SAC 2010, Waterloo, Ontario, Canada, August 12-13, 2010, Revised Selected Papers. Lecture Notes in Computer Science. Vol. 6544. pp. 74–91. doi:10.1007/978-3-642-19574-7_5. ISBN 978-3-642-19573-0.
- ^ Green, Matthew (12 March 2013). “Attack of the week: RC4 is kind of broken in TLS”. Cryptography Engineering. Archived from the original on March 14, 2013. Retrieved March 12, 2013.
- ^ Nadhem AlFardan, Dan Bernstein, Kenny Paterson, Bertram Poettering and Jacob Schuldt. “On the Security of RC4 in TLS”. Royal Holloway University of London. Archived from the original on March 15, 2013. Retrieved March 13, 2013.{{cite web}}: CS1 maint: multiple names: authors list (link)
- ^ AlFardan, Nadhem J.; Bernstein, Daniel J.; Paterson, Kenneth G.; Poettering, Bertram; Schuldt, Jacob C. N. (8 July 2013). “On the Security of RC4 in TLS and WPA” (PDF). Archived (PDF) from the original on 22 September 2013. Retrieved 2 September 2013. {{cite journal}}: Cite journal requires |journal= (help)
- ^ AlFardan, Nadhem J.; Bernstein, Daniel J.; Paterson, Kenneth G.; Poettering, Bertram; Schuldt, Jacob C. N. (15 August 2013). On the Security of RC4 in TLS (PDF). 22nd USENIX Security Symposium. p. 51. Archived (PDF) from the original on 22 September 2013. Retrieved 2 September 2013. Plaintext recovery attacks against RC4 in TLS are feasible although not truly practical
- ^ Goodin, Dan (15 July 2015). “Once-theoretical crypto attack against HTTPS now verges on practicality”. Ars Technical. Conde Nast. Archived from the original on 16 July 2015. Retrieved 16 July 2015.
- ^ “Mozilla Security Server Side TLS Recommended Configurations”. Mozilla. Archived from the original on 2015-01-03. Retrieved 2015-01-03.
- ^ “Security Advisory 2868725: Recommendation to disable RC4”. Microsoft. 2013-11-12. Archived from the original on 2013-11-18. Retrieved 2013-12-04.
- ^ “Ending support for the RC4 cipher in Microsoft Edge and Internet Explorer 11”. Microsoft Edge Team. September 1, 2015. Archived from the original on September 2, 2015.
- ^ Langley, Adam (Sep 1, 2015). “Intent to deprecate: RC4”.
- ^ Barnes, Richard (Sep 1, 2015). “Intent to ship: RC4 disabled by default in Firefox 44”. Archived from the original on 2011-01-22.
- ^ a b John Leyden (1 August 2013). “Gmail, Outlook.com and e-voting ‘pwned’ on stage in crypto-dodge hack”. The Register. Archived from the original on 1 August 2013. Retrieved 1 August 2013.
- ^ “BlackHat USA Briefings”. Black Hat 2013. Archived from the original on 30 July 2013. Retrieved 1 August 2013.
- ^ Smyth, Ben; Pironti, Alfredo (2013). Truncating TLS Connections to Violate Beliefs in Web Applications. 7th USENIX Workshop on Offensive Technologies (report). Archived from the original on 6 November 2015. Retrieved 15 February 2016.
- ^ Goodin, Dan (26 July 2016). “New attack bypasses HTTPS protection on Macs, Windows, and Linux”. Ars Technica. Condé Nast. Archived from the original on 27 July 2016. Retrieved 28 July 2016.
- ^ Goodin, Dan (August 24, 2016). “HTTPS and OpenVPN face new attack that can decrypt secret cookies”. Ars Technica. Archived from the original on August 24, 2016. Retrieved August 24, 2016.
- ^ “Why is it called the ‘Heartbleed Bug’?”. The Washington Post. 2014-04-09. Archived from the original on 2014-10-09.
- ^ “Heartbleed Bug vulnerability [9 April 2014]”. Comodo Group. Archived from the original on 5 July 2014.
- ^ Bleichenbacher, Daniel (August 2006). “Bleichenbacher’s RSA signature forgery based on implementation error”. Archived from the original on 2014-12-16.
- ^ “BERserk”. Intel Security: Advanced Threat Research. September 2014. Archived from the original on 2015-01-12.
- ^ Goodin, Dan (February 19, 2015). “Lenovo PCs ship with man-in-the-middle adware that breaks HTTPS connections”. Ars Technica. Archived from the original on September 12, 2017. Retrieved December 10, 2017.
- ^ Valsorda, Filippo (2015-02-20). “Komodia/Superfish SSL validation is broken”. Filippo.io. Archived from the original on 2015-02-24.
- ^ a b Goodin, Dan (26 May 2016). “”Forbidden attack” makes dozens of HTTPS Visa sites vulnerable to tampering”. Ars Technica. Archived from the original on 26 May 2016. Retrieved 26 May 2016.
- ^ Clark Estes, Adam. “Everything You Need to Know About Cloudbleed, the Latest Internet Security Disaster”. Gizmodo. Archived from the original on 2017-02-25. Retrieved 2017-02-24.
- ^ Diffie, Whitfield; van Oorschot, Paul C; Wiener, Michael J. (June 1992). “Authentication and Authenticated Key Exchanges”. Designs, Codes and Cryptography. 2 (2): 107–125. CiteSeerX 10.1.1.59.6682. doi:10.1007/BF00124891. S2CID 7356608. Archived from the original on 2008-03-13. Retrieved 2008-02-11.
- ^ “Discussion on the TLS mailing list in October 2007”. Archived from the original on 22 September 2013. Retrieved 20 February 2022.
- ^ “Protecting data for the long term with forward secrecy”. Archived from the original on 2013-05-06. Retrieved 2012-11-05.
- ^ Bernat, Vincent (28 November 2011). “SSL/TLS & Perfect Forward Secrecy”. Archived from the original on 2012-08-27. Retrieved 2012-11-05.
- ^ “SSL Labs: Deploying Forward Secrecy”. Qualys.com. 2013-06-25. Archived from the original on 2013-06-26. Retrieved 2013-07-10.
- ^ Ristic, Ivan (2013-08-05). “SSL Labs: Deploying Forward Secrecy”. Qualsys. Archived from the original on 2013-09-20. Retrieved 2013-08-31.
- ^ a b Langley, Adam (27 June 2013). “How to botch TLS forward secrecy”. imperialviolet.org. Archived from the original on 8 August 2013.
- ^ a b Daignière, Florent. “TLS “Secrets”: Whitepaper presenting the security implications of the deployment of session tickets (RFC 5077) as implemented in OpenSSL” (PDF). Matta Consulting Limited. Archived (PDF) from the original on 6 August 2013. Retrieved 7 August 2013.
- ^ a b Daignière, Florent. “TLS “Secrets”: What everyone forgot to tell you…” (PDF). Matta Consulting Limited. Archived (PDF) from the original on 5 August 2013. Retrieved 7 August 2013.
- ^ L.S. Huang; S. Adhikarla; D. Boneh; C. Jackson (2014). “An Experimental Study of TLS Forward Secrecy Deployments”. IEEE Internet Computing. 18 (6): 43–51. CiteSeerX 10.1.1.663.4653. doi:10.1109/MIC.2014.86. S2CID 11264303. Archived from the original on 20 September 2015. Retrieved 16 October 2015.
- ^ “Protecting data for the long term with forward secrecy”. Archived from the original on 2014-02-12. Retrieved 2014-03-07.
- ^ Hoffman-Andrews, Jacob. “Forward Secrecy at Twitter”. Twitter. Archived from the original on 2014-02-16. Retrieved 2014-03-07.
- ^ a b c Durumeric, Zakir; Ma, Zane; Springall, Drew; Barnes, Richard; Sullivan, Nick; Bursztein, Elie; Bailey, Michael; Halderman, J. Alex; Paxson, Vern (5 September 2017). “The Security Impact of HTTPS Interception”. NDSS Symposium. doi:10.14722/ndss.2017.23456. ISBN 978-1-891562-46-4.
- ^ a b These certificates are currently X.509, but RFC 6091 also specifies the use of OpenPGP-based certificates.
- ^ “tls – Differences between the terms “pre-master secret”, “master secret”, “private key”, and “shared secret”?”. Cryptography Stack Exchange. Retrieved 2020-10-01.
- ^ Chris (2009-02-18). “vsftpd-2.1.0 released – Using TLS session resume for FTPS data connection authentication”. Scarybeastsecurity. blogspot.com. Archived from the original on 2012-07-07. Retrieved 2012-05-17.
- ^ Valsorda, Filippo (23 September 2016). “An overview of TLS 1.3 and Q&A”. The Cloudflare Blog.
- ^ Wildcard SSL Certificate overview, archived from the original on 2015-06-23, retrieved 2015-07-02
- ^ Named-based SSL virtual hosts: how to tackle the problem (PDF), archived (PDF) from the original on 2012-08-03, retrieved 2012-05-17
Further reading
| Wikimedia Commons has media related to SSL and TLS. |
- Wagner, David; Schneier, Bruce (November 1996). “Analysis of the SSL 3.0 Protocol” (PDF). The Second USENIX Workshop on Electronic Commerce Proceedings. USENIX Press. pp. 29–40.
- Eric Rescorla (2001). SSL and TLS: Designing and Building Secure Systems. United States: Addison-Wesley Pub Co. ISBN 978-0-201-61598-2.
- Stephen A. Thomas (2000). SSL and TLS essentials securing the Web. New York: Wiley. ISBN 978-0-471-38354-3.
- Bard, Gregory (2006). “A Challenging But Feasible Blockwise-Adaptive Chosen-Plaintext Attack on SSL”. International Association for Cryptologic Research (136). Retrieved 2011-09-23.
- Canvel, Brice. “Password Interception in a SSL/TLS Channel”. Retrieved 2007-04-20.
- IETF Multiple Authors. “RFC of change for TLS Renegotiation”. Retrieved 2009-12-11.
- Creating VPNs with IPsec and SSL/TLS Linux Journal article by Rami Rosen
- Joshua Davies (2010). Implementing SSL/TLS. Wiley. ISBN 978-0470920411.
- Polk, Tim; McKay, Kerry; Chokhani, Santosh (April 2014). “Guidelines for the Selection, Configuration, and Use of Transport Layer Security (TLS) Implementations” (PDF). National Institute of Standards and Technology. Archived from the original (PDF) on 2014-05-08. Retrieved 2014-05-07.
- Abdou, AbdelRahman; van Oorschot, Paul (August 2017). “Server Location Verification (SLV) and Server Location Pinning: Augmenting TLS Authentication”. Transactions on Privacy and Security. ACM. 21 (1): 1:1–1:26. doi:10.1145/3139294. S2CID 5869541.
- Ivan Ristic (2022). Bulletproof TLS and PKI, Second Edition. Feisty Duck. ISBN 978-1907117091.
External links
- IETF (Internet Engineering Task Force) TLS Workgroup